 Role Availability Role Availability
|
 Read-Only Read-Only
|
 Investigator Investigator |
 Analyst Analyst
|
 Manager Manager
|
USM Anywhere enables you to make the sensor Sensors are deployed into an on-premises, cloud, or multi-cloud environment to collect logs and other security-related data. This data is normalized and then securely forwarded to USM Anywhere for analysis and correlation. drops future events Any traffic or data exchange detected by AT&T Cybersecurity products through a sensor or external devices such as a firewall. that match the rule. These events will be neither correlated nor stored. Through these rules, you can define which event data you are going to store in USM Anywhere. You will pay for the data you use.
Note: Filtering rules is not retroactive. The rule applies to future items, but not to to previous items, even if those items follow the rule.
Important: You can't use a correlation list when you create a filtering rule.
To create a filtering rule from the Events page
- Go to Activity > Events.
-
Search the events which you want to include in the filtering rule.
See Searching Events for more information.
- Click one of them.
- Select Create Rule > Create Filtering Rule.
-
Select a Boolean operator.
The options are AND, OR, AND NOT, and OR NOT.
-
Select a packet type in the Match drop-down list.
- Logs: Use this packet type for event-based rules.
- Configuration Issues: Use this packet type for configuration issues-based rules1.
- Vulnerabilities: Use this packet type for vulnerabilities-based rules.
- Alarms: Use this packet type for console user alarms-based rules.
- You have already suggested property values to create a matching condition. If you want to add new property values, click Add Condition.
-
(Optional.) Click Add Group to group your conditions.
Note: See Operators in the Orchestration Rules for more information.
- Click Next.
- Enter a name for the rule.
- (Optional.) Enter a description for identifying this rule.
-
Click Save.
Note: If the field is related to the name of a country, you should use the country code defined by the ISO 3166.
Note: The Sources or Destinations field needs to match the universally unique identifier (UUID) of the event or alarm. You can use the Source Name or Destination Name field instead.
Important: Instead of using the equals and equals, case insensitive operators for array fields, AT&T Cybersecurity recommends the use of the in or contains operators.
Note: If you need to add a property value that maps with a property key, you need to know the mapping of the field. See Determining the Mapping of a Field for more information.
Note: The current rule box shows you the syntax of your rule, and the rule verification box reviews that syntax before saving the rule.
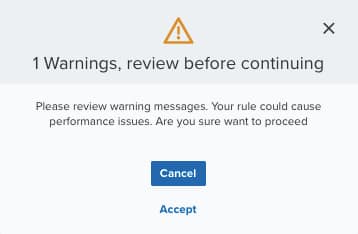
Important: A dialog box opens if there are warning messages. Click Cancel to review the warning messages, or click Accept to continue creating the rule.
The created rule displays in the list of rules. You can see it from Settings > Rules. See Orchestration Rules for more information.
Important: It takes a few minutes for an orchestration rule to become active.

 Feedback
Feedback