An alarm in AlienVault USM Appliance consists of one or more events, based on one of the following:
-
One or more out-of-the-box directives, or rules, performed by the correlation engine of the USM Appliance Server. These look at and connect multiple events to assess their relative priority and reliability .The events then get re-injected into the USM Appliance Server process as though they were coming from the USM Appliance Sensor. For more information about correlation rules, see Correlation Rules .
-
Elevated parameters that USM Appliance evaluates, based on existing policy configurations and event risk. An alarm is generated when the risk of an event is >= 1. Because risk is calculated as Risk = asset value * reliability * priority / 25, the likelihood of an alarm will be influenced by the asset or network value. It is important to consider correlation settings in regard to risk values, as you may want multiple directive rules depending on reliability and asset values. For more information about directives, see Event Correlation.
Depending on how your policies are configured, this can account for alarms coming from various sources. For example, policies set up in the Default policy group can process alarms from events, while Policies for events generated in the server will only target server events. For more information about policy groups, see The Policy View.
-
Alarms are generated and processed differently for events related to OTX pulses. For more information, see Viewing OTX Alarms.
When you select the Analysis > Alarms option, USM Appliance displays the following page.
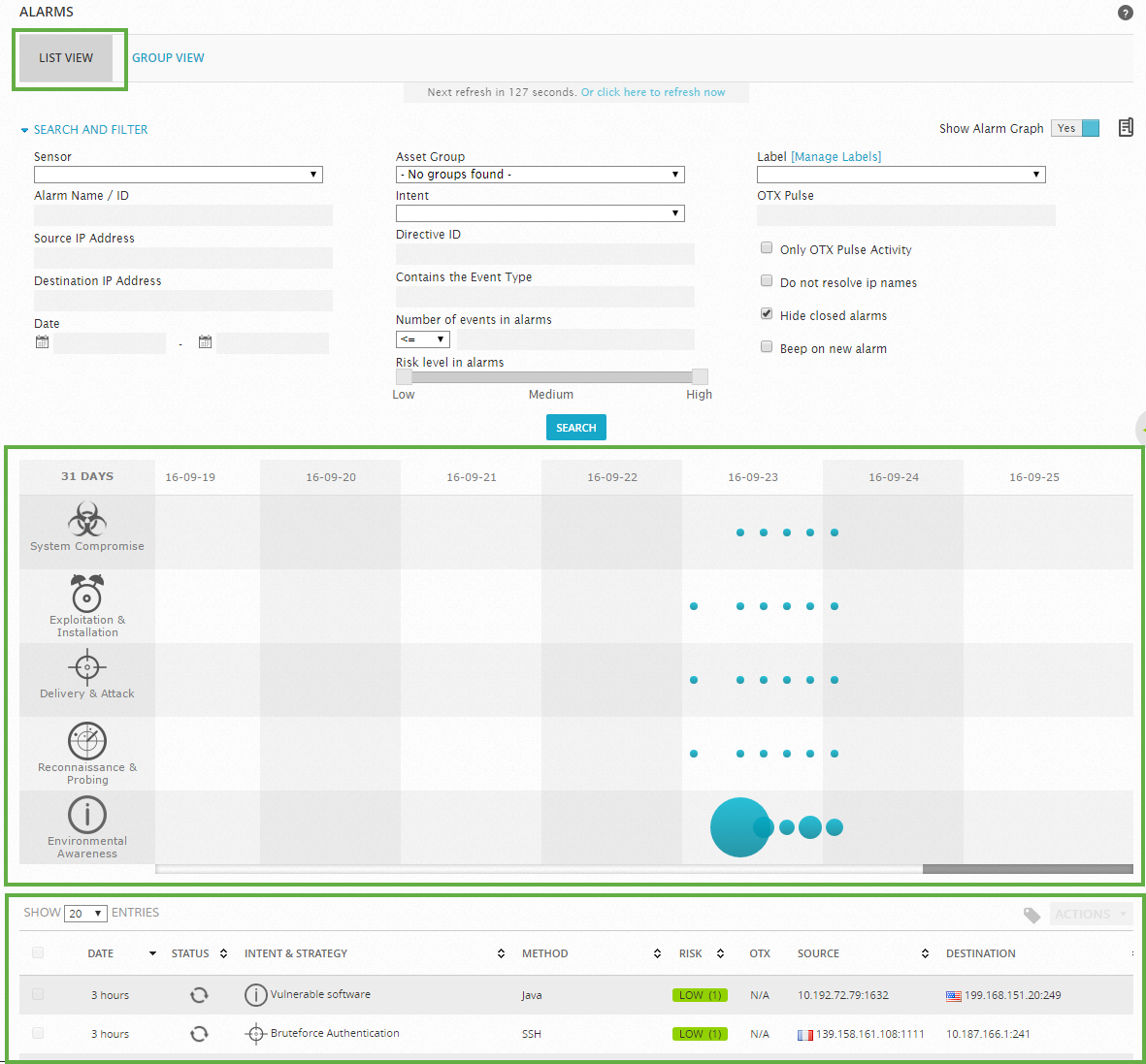
By default, the display opens in List View, which simply lists alarms in reverse chronological order (the latest issued alarm is displayed first). You can also change the display to Group View, which allows you to group alarms by different keys such as alarm name, source and destination IP address, or alarm type.
The middle portion of the screen includes a table that provides a graphical aggregated representation of alarms based on directive events Security event created from a correlation directive when all the conditions specified in the correlation rule are matched., which are events generated by the USM Appliance Server. The table contains such alarms occurred in the last 31 days; each column represents a different day. Blue circles indicate the number of times that an alarm in a category appeared. A bigger circle indicates a higher number of alarms were generated. You can mouse over each of the circles to get the actual number of different types of alarms that occurred as well as a Top 5 list of possible remedies for each alarm type.
Alarms are sorted into five different categories, which are represented by the graphic icons in the display. These are:
- System compromise (
 )
) - Exploitation and installation (
 )
) - Delivery and attack (
 )
) - Reconnaissance and probing (
 )
) - Environmental awareness (
 )
)
The categories are also consistent with the sequence or stages of events that an attacker might follow to successfully infiltrate a network, gain unauthorized access to data, or perform some malicious act. The categories are also consistent with a model of attack detailed by Lockheed Martin called the Cyber Kill Chain.
Below the categorized display of alarm icons, USM Appliance displays a tabular listing of individual alarms, by default, in reverse chronological order. In addition, if you click on any of the blue circles, USM Appliance will display only the alarms corresponding to the selected circle. From the list of alarms, you can click on any individual alarm row to expand the display of information about the alarm. You can then click the View Details button, or click the ![]() icon, to display more information on the selected alarm, including individual events that actually triggered the alarm.
icon, to display more information on the selected alarm, including individual events that actually triggered the alarm.
The top section of the Alarms page display lets you search for and filter alarms that are displayed on the Alarms page. You can qualify alarms by event attributes such as sensor location, asset group, risk level, or OTX pulse.
AlienVault OSSIM Limitations: Alarms in AlienVault OSSIM lack the built-in context provided in USM Appliance. The work compiled by the AT&T Alien Labs™ Security Research Team to analyze and validate OTX threat data is available in bothUSM Appliance and AlienVault OSSIM.
 Feedback
Feedback