| Applies to Product: |
|
|
AlienVault NIDS plays an important role in the USM Appliance. By detecting malicious network events, it provides vital information for correlation directives and cross-correlation rules. Combining this information with the events collected from other devices, USM Appliance presents a complete picture of the malicious activity.
The AlienVault NIDS functionality, including monitoring network traffic and detecting malicious events, takes place on the USM Appliance Sensor. You should configure at least two network interfaces on a USM Appliance Sensor or USM Appliance All-in-One:
- Management interface — Configure the interface with an IP address, which you can reach from the network. Use this interface for administrative purposes and communication with other USM Appliance components. See Set Up the Management Interface.
- Network monitoring interface — Do not configure an IP address on the interface. Instead, connect the interface to a spanned or mirrored port on a network switch , so that USM Appliance can examine the throughput. You can use more than one network monitoring interface to observe several networks from a single USM Appliance Sensor. See Configuring AlienVault NIDS.
The USM Appliance Server consumes the NIDS signatures through plugins, which generates the AlienVault NIDS events. The correlation engine processes and correlates the normalized events, then stores them in the SIEM database.
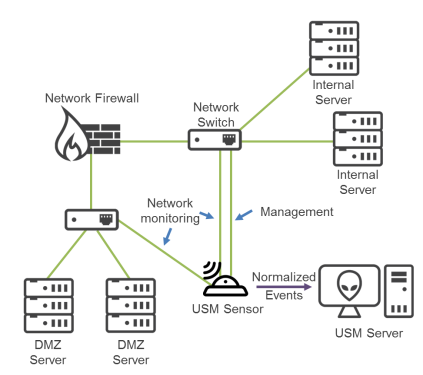
AlienVault NIDS diagram
AlienVault OSSIM Limitations: Both AlienVault OSSIM and the USM Appliance HIDS decoders are fully featured, with all of their information coming from the Plugin Feed Updates that USM Appliance and AlienVault OSSIM provide. However, AlienVault OSSIM lacks the depth of NIDS information that is provided to USM Appliance through the Threat Intelligence Updates.
 Feedback
Feedback