| Applies to Product: |
|
|
Policy Consequences are the final component to creating a policy, after Create a New Policy and Create Policy Conditions. Policy Conditions are assigned at the bottom of the Policy's page.
External event consequences can be consist of any of the following. You may assign more than one consequence to a policy.
- Actions — Use an Action as a Consequence to a Policy
- SIEM — Adjust SIEM Consequences to Process Events
- Logger — Create a Consequence to Log and Sign Events
- Forwarding — Create a Consequence to Forward Events
Note: For a directive event, the Logger cannot be configured as a consequence.
Use an Action as a Consequence to a Policy
This task assumes that you or someone else has already created an action that you can reference. For instructions on how to create an action, see Create an Action.
To add an Action to a consequence
- Go to Configuration > Threat Intelligence > Policy and, in the policy you are creating or modifying, click Actions under Consequences.
-
Select the action from the Available Actions, at right, and add it by clicking the plus (+) sign, or by dragging it to the Active Actions section.
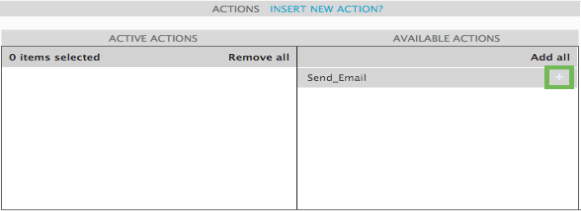
Now the action you selected appears in the Actions area of Consequences at the top of the page.
Adjust SIEM Consequences to Process Events
You can choose to make a SIEM consequence for a deeper control over risk assessment, event priority, and correlations. For more details on SIEM as a policy consequence, see SIEM in Policy Consequences.
To create a SIEM consequence to a policy condition
-
Go to Configuration > Threat Intelligence > Policy and, in the policy you are creating or modifying, click SIEM under Consequences.
A SIEM window opens under Policy Consequences at the bottom of the page.
-
Fill out the form as appropriate.
- SIEM — Select Yes for SIEM as a consequence.
- Set Event Priority — From the Event Priority list, select the priority you want USM Appliance to assign to such events. Event priority is from 1 to 5, with 1 being minor and 5 being major, or an attack in progress.
-
Risk Assessment — Indicate whether or not you want USM Appliance to perform risk assessment as a consequence of this policy by selecting Yes or No.
Risk assessment looks at asset value, event priority, and event reliability. It then assigns a risk based on the value of the asset and type of event.
-
Logical Correlation — Indicate whether or not you want to use logical correlation by selecting Yes or No.
You use this to create new events from multiple events found by detectors and monitors. These are configured using correlation directives (logical trees combining individual events). Each new event has assigned priority and reliability values define by one directive.
-
Cross-Correlation — Indicate whether or not you want to enable cross-correlation by selecting Yes or No.
-
SQL Storage — Indicate whether or not you want to enable SQL storage by selecting Yes or No.
Events detected or generated by USM Appliance are stored in the SQL database by default. Enabling SQL storage means that events matching a policy setting should be stored in the SQL database as well.
Note: It is not required nor desirable for all events to be stored in the database.
Now the SIEM parameters you selected appear in the SIEM area of Consequences at the top of the page.
Important: Your changes in the policy will override the default configurations under Configuration > Deployment > Components > Servers.
Create a Consequence to Log and Sign Events
By adding a log consequence to your policy, events processed by policies will be sent to the Logger for analysis, compliance, and archiving purposes.
To enable the USM Appliance Logger to log events processed by specific policies
- Go to Configuration > Threat Intelligence > Policy and, in the policy you are creating or modifying, click the colored Logger section under Consequences.
A Logger window opens under Policy Consequences at the bottom of the page.
- To enable the Logger to store events caught by your policy (to the local logger), select Yes.
Next to Sign, you can see that either Line or Block are selected. (For a detailed explanation of what these do, see Logger in Policy Consequences.)
Create a Consequence to Forward Events
By enabling the Forwarding consequence, you instruct USM Appliance to forward all or a subset of events, for example, from a remote USM Appliance Server, to a headquarters USM Appliance Server.
To enable event forwarding
-
Go to Configuration > Threat Intelligence > Policy and, in the policy you are creating or modifying, click the colored Forwarding section under Consequences.
A Forwarding window opens under Policy Consequences at the bottom of the page.
-
Select Yes to enable forwarding or No to disable forwarding.
If you select Yes, then select the server you want to forward to.
Warning: Having Logger set to Yes and Forwarding set to No in a policy consequence will send all events to the local logger. This takes precedence over what is configured under Configuration > Deployment > Components > Servers (as documented in Configure the USM Appliance Logger after Deployment) for all events that fall under the policy's conditions.
 Feedback
Feedback