Leverage OTX to the Fullest with AlienVault USM™
SEE FOR YOURSELF:
Put USM to Work in Your Environment
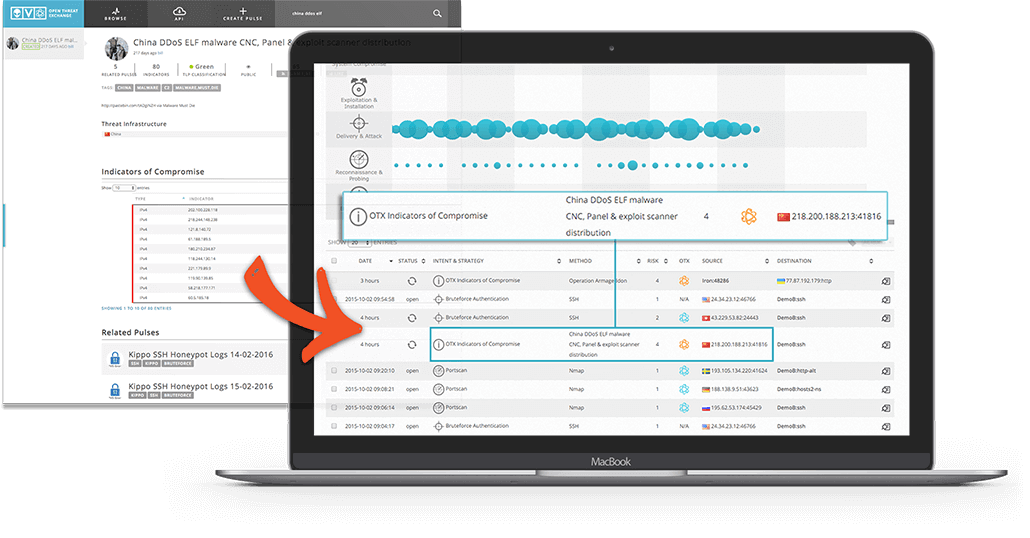
AlienVault’s Open Threat Exchange (OTX) provides a wealth of intelligence about the latest threats reported by the threat-sharing community and by the AlienVault Labs threat research team. AlienVault’s Unified Security Management (USM) platform makes the threat intelligence easily actionable by integrating it with five essential security capabilities – asset discovery, vulnerability assessment, intrusion detection, behavioral monitoring, and SIEM. The AlienVault USM Threat Intelligence subscription tunes these five essential security controls to keep USM’s threat detection capabilities up to date with the latest threats, and provide you with detailed information on what the threat is, where it’s originating from, which assets in your environment are at risk, and how to respond.
Leveraging information from OTX and enhancing it with AlienVault’s proprietary data, the AlienVault Labs team continuously updates eight coordinated rulesets in the USM platform, including:
- Correlation Directives – USM ships with over 3,000 pre-defined rules that translate behavioral patterns into specific, actionable threat information by linking disparate events from across your network
- Network IDS Signatures – detect the latest malicious traffic on your network
- Host IDS Signatures – identify the latest threats targeting your critical systems
- Asset Discovery Signatures – detect the latest operating systems, applications, and device information
- Vulnerability Assessment Signatures – uncover the latest vulnerabilities on your systems
- Reporting Modules – receive new views of critical data about your environment to management and satisfy auditor requests
- Dynamic Incident Response Templates – customized guidance on how to respond to each alert
- Newly Supported Data Source Plugins – expand your monitoring footprint by integrating data from legacy security devices and applications
These rulesets, in coordination with the built-in security controls integrated into USM, provide unparalleled threat detection, eliminating the need for you to spend precious time conducting your own research on emerging threats and tuning your systems on your own to detect them.
Existing USM & OSSIM
Users, Get Started Now!
Learn more about how to connect OTX to
USM or OSSIM.
New to AlienVault?
Download a free 30-day trial of AlienVault
USM to check it out!