Accelerate and automate threat detection
One platform for threat detection, incident response, and compliance.
Advanced Threat Detection Anywhere Modern Threats Appear
Your organization’s security depends on your ability to rapidly detect and respond to emerging threats across your cloud and on-premises environments. Yet, attack methods and strategies evolve constantly, making threat detection an always-moving target.
Most organizations simply don’t have the resources or time to extensively research the global threat landscape for the latest attack vectors, nor can they spend time analyzing every indicator that an attack is happening.
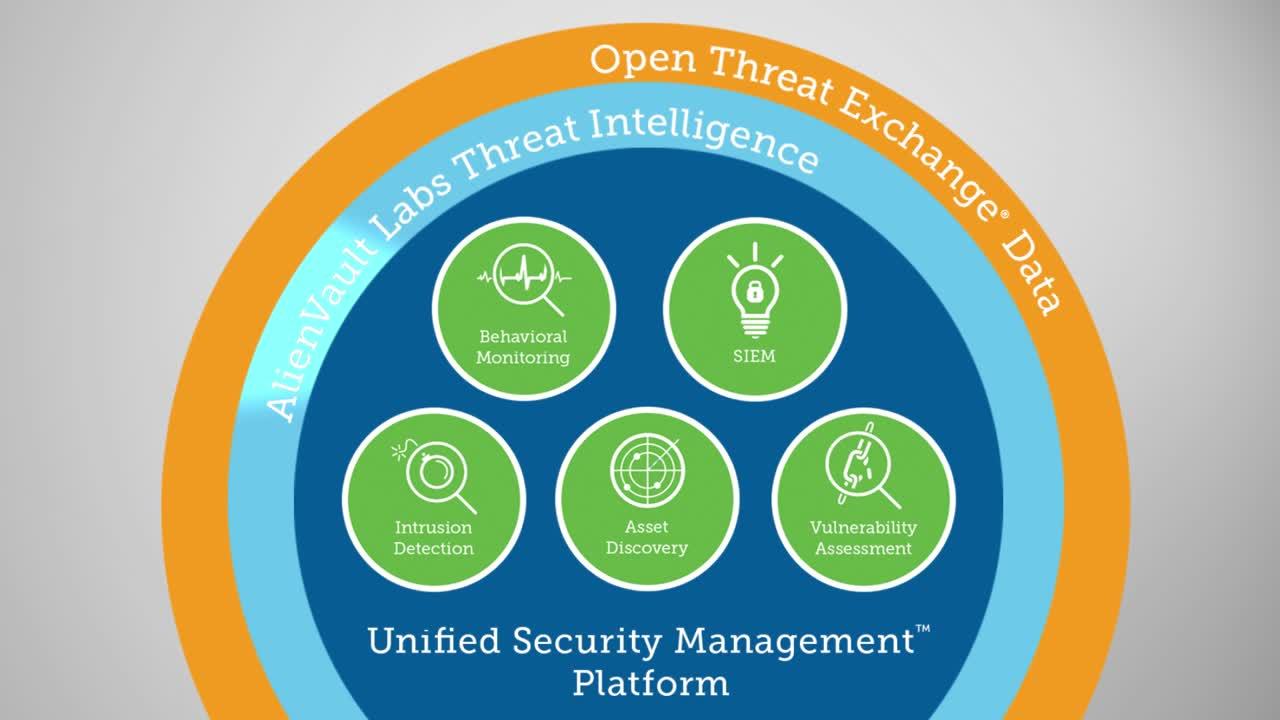
Unified Security Management® (USM) is built with these organizations in mind. USM performs advanced threat detection across your cloud and on-premises environments. It combines multiple essential security capabilities – asset discovery, vulnerability assessment, intrusion detection, behavioral monitoring, endpoint detection and response, SIEM event correlation, and log management – in one unified console. This gives you everything you need to quickly identify, analyze, and respond to emerging threats–in one cost-effective and easy-to-use solution.
In addition, the Alien Labs Security Research Team works on your behalf to research the latest global threats and vulnerabilities, and delivers threat intelligence updates continuously into the USM platform. That way, you get the assurance of an always-up-to-date and optimally performing security monitoring solution, even without a dedicated in-house security team.
Alien Labs leverages threat intelligence from the Open Threat Exchange® (OTX™)—the world’s largest open threat intelligence community of security experts, researchers, and IT professionals worldwide who provide global insight into the latest attack trends, bad actors, indicators of compromise, and affected industries.
Focus on the Threats That Matter Right Now
- Quickly assess threats with automated alert prioritization
- Make informed decisions with full details on every alarm, including a description of the threat, its method and strategy, and recommendations on response
Get Compete Threat Visibility with All-in-One Security Essentials
- Achieve multi-layered threat detection for your on-premises and cloud environments using the USM platform’s built-in host-, network-, and cloud-based intrusion detection systems and endpoint detection capabilities
- Easily search and analyze threats with a consolidated view of your assets, vulnerabilities, and malicious activities in your environment
- Eliminate your security blind spots by aggregating and correlating events from all your devices, servers, endpoints, and applications, as well as monitoring user and administrator activities
Stay Vigilant with Continuous Threat Intelligence Delivered
- Receive continuous, curated threat intelligence from Alien Labs Security Research Team, delivered automatically to the USM platform
- Leverage threat data from the world’s largest open threat intelligence community—OTX
- Stay ahead of emerging threats with correlation rules that are continually and automatically updated with the latest threat intelligence
Focus on the Threats that Matter Right Now
With the constantly evolving nature of the threat landscape, it can be difficult—especially with limited resources—to address every incident and alert that occurs in and across your on-premises and cloud environments. Instead, you must be able to cut through the clutter of alerts and false positives to effectively prioritize your threat detection and response activities.
USM Anywhere automatically prioritizes the most severe threats facing your environment. The platform uses the Kill Chain Taxonomy to categorize threats by severity in a highly visual and instantly recognizable way, so that you can immediately know which threats to focus on first. It also provides you with contextual information to help you understand attack intent and threat severity, based on how the threats are interacting with your environment.
- System Compromise – Behavior indicating a compromised system. This is the most severe threat level.
- Exploitation & Installation – Behavior indicating a successful exploit of a vulnerability or backdoor/RAT being installed on a system.
- Delivery & Attack – Behavior indicating an attempted delivery of an exploit.
- Reconnaissance & Probing – Behavior indicating a bad actor attempting to discover information about your network.
- Environmental Awareness – Behavior indicating policy violations, vulnerable software, or suspicious communications.
Get Compete Threat Visibility with All-in-One Security Essentials
USM provides multiple essential security capabilities to help identify, understand, and contain threats—all through a single pane of glass. With all security-related data about your assets, vulnerabilities, and intrusions centralized and easily searchable, and backed by threat intelligence from Alien Labs and OTX, you can investigate faster and respond sooner to risks and threats against your critical infrastructure.
Asset Discovery
- Discovery of assets across on-premises, cloud, and hybrid environments
- Identification of software & services deployed on each asset
- Ability to group assets, supporting simplified monitoring and review
Vulnerability Assessment
- Scans for vulnerabilities across all your monitored environments
- Prioritization based on the severity of the vulnerability, so you can prioritize response
- Indication of any available patches for identified vulnerabilities
Endpoint Detection and Response
- Maintain continuous visibility of your endpoints in the cloud, on premises, and remote
- Get built-in file integrity monitoring (FIM) to monitor changes to critical files and registries as required by many regulatory compliance standards
- Proactively query endpoints for information needed for forensics investigations
Intrusion Detection
- Cloud IDS (CIDS)
- Network IDS (NIDS)
- Host IDS (HIDS)
USM delivers multi-layered IDS for your cloud, hybrid cloud, and on-premises environments threat detection needs. Built-in network intrusion detection (NIDS), host intrusion detection (HIDS), and native cloud intrusion detection (CIDS) capabilities work in concert, giving you comprehensive intrusion detection across your entire IT landscape and eliminating your security blind spots.
Behavioral Monitoring
- Monitor cloud access and activity logs (Azure: Monitor, AWS: CloudWatch, CloudTrail, S3, ELB, VMware and Hyper-V access logs)
- Monitor user and administrator activities on systems and applications, including Okta, Active Directory, Office 365, and G Suite
- AWS VPC Flow Monitoring
Incident Response Guidance
- Review context on the threat, including details on strategy, method, and actor
- See enriched information on the incident from the Open Threat Exchange (OTX), with links to ‘pulses’ from the OTX community
- Review the affected asset, including details about what software and services are installed, and any other related vulnerabilities and alarms
- Identify the destination IP address or domain to which communications are being passed (e.g. a Command & Control Server)
- Recommended actions to take for further investigation and threat containment
SIEM & Log Management
- Event correlation by graph-based machine learning and finite-state machine (FSM) correlation engines
- Integrated threat intelligence, including updated correlation directives, from Alien Labs Security Team, and the Open Threat Exchange (OTX)
- Aggregation of logs from all servers, endpoints, and applications across your on-premises, cloud, and hybrid environments
- Up to 90 days of searchable events stored within fast, Elasticsearch storage
- At least 12-months of raw log retention