Network vulnerability assessment
Everything you need to accelerate vulnerability assessment, threat detection, and incident response.
Find the Vulnerabilities on Your Network Before Attackers Do
With network vulnerability assessment, you can find the weak spots in your critical assets and take corrective action before attackers exploit them to sabotage your business or steal your confidential data.
Constant application updates and changes to application and system configurations can introduce vulnerabilities and leave you susceptible to an attack, even if you are keeping your security controls up to date. To keep your data secure, you must continuously scan your systems and devices to detect vulnerabilities as they arise.
Once detected, you must assess the potential threat of those vulnerabilities and prioritize your remediation activities to deal with the greatest threats first. This is no small task, as you must consider multiple factors:
- How business-critical or sensitive is the vulnerable asset?
- Have any intrusions or exploits been attempted on the vulnerable asset?
- How is the vulnerability being exploited by attackers in the wild?
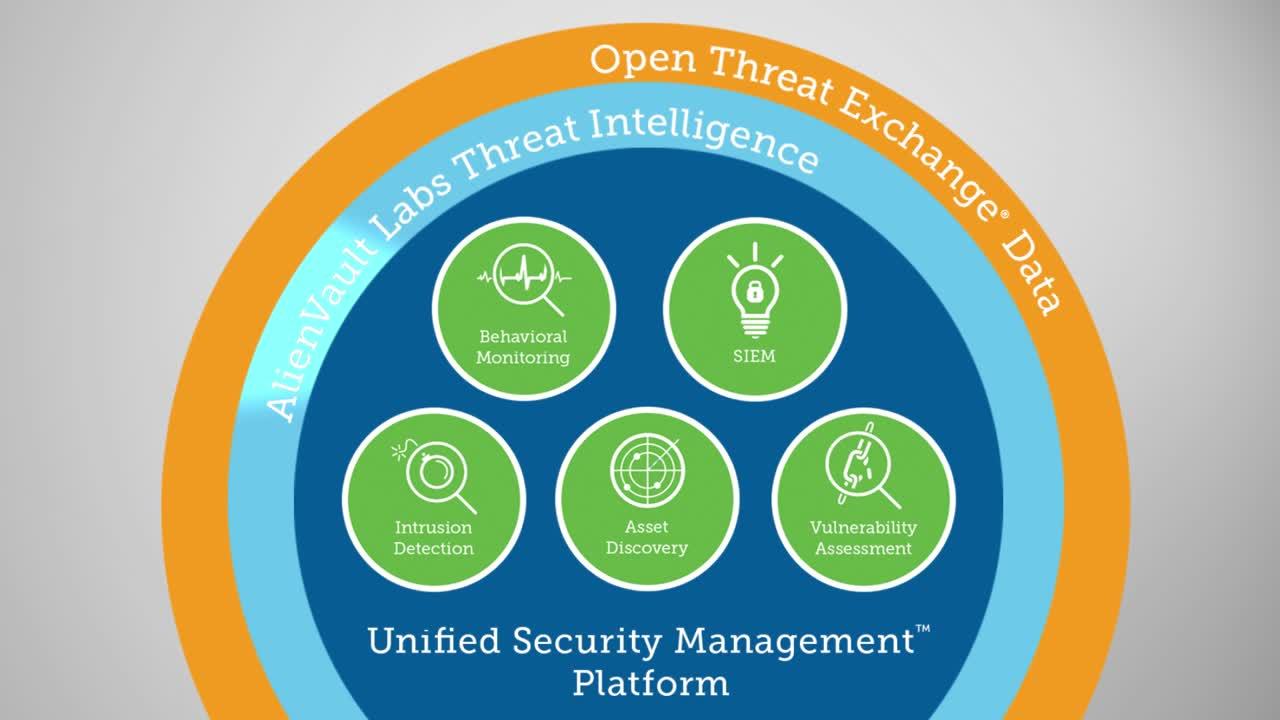
Unified Security Management® (USM) provides all this information in a single pane of glass, so you can easily perform network vulnerability assessment in your cloud, on-premises, and hybrid environments. It brings together essential security capabilities—asset discovery and inventory, vulnerability assessment, intrusion detection, behavioral monitoring, SIEM, and log management—all in a unified, easy-to-use platform. In addition, continuous threat intelligence, including vulnerability signatures, is delivered directly from Alien Labs Security Research Team, backed by the Open Threat Exchange® (OTX™).
Continuously Scan and Monitor Your Environments
- Easily set up network vulnerability assessment scans targeting individual assets, asset groups, or even entire networks
- Schedule vulnerability assessment scans to run automatically at regular intervals so you don’t have to manage your scanning routine manually
- Meet security best practices and regulatory requirements for frequent detection of assets and scanning for vulnerabilities
- See all assets in your environments and where they are most vulnerable
Remediate Your Vulnerabilities Faster
- Use graphically-rich dashboards, pre-built reports, and customizable data views to quickly identify where vulnerabilities exist across your environments
- Review vulnerabilities by their severity, so you can better prioritize your response
- Quickly identify the availability of any patches, reducing the time you would typically need to research how to remediate the risk from the vulnerability
Receive Regular Updates to Vulnerability-Related Threat Intelligence
- Receive continuously updated vulnerability signatures from the Alien Labs Security Research Team
- Identify the history of vulnerabilities on assets and the availability of any patches
- Investigate vulnerabilities and threats deeper with links to CVE reports in the Open Threat Exchange (OTX)
Continuously Scan and Monitor Your Environments
Effective network vulnerability assessment demands that you continuously scan and monitor your critical assets. For example, virtualization has simplified the process to spin up new assets in public and private cloud environments, and so it’s easier to miss assets that are offline during monthly or quarterly vulnerability scans. If not regularly assessed for vulnerabilities, these assets can drive up your threat exposure and leave you vulnerable to attacks.
USM makes continuous network vulnerability assessment a simple yet flexible process. Because the USM platform includes asset discovery and inventory, you always have the most accurate, up-to-date asset inventory against which USM can run vulnerability scans.
USM supports the following network vulnerability scanning capabilities:
Regularly Scheduled Auto-scanning
Create scans that run daily, weekly, or monthly during your off-peak hours. Automated scanning ensures continuous visibility of your vulnerabilities as your IT landscape changes. You can also re-run scans, modify scanning schedules, or even delete jobs – all from within the USM user interface.
Authenticated Scanning
Authenticated scans perform vulnerability assessment by using host credentials to investigate your assets, looking for vulnerable software packages, local processes, and services running on the system. For example, with Windows servers, you can monitor registry keys and files, looking for traces of infiltration.

Remediate Your Vulnerabilities Faster
While standalone vulnerability assessment software scans and detects vulnerabilities, it does not give you all the information you need to efficiently prioritize your response. To assess whether a vulnerability requires urgent action or not, you need to know:
- Is the vulnerable asset business critical or does it contain highly sensitive data?
- Is this vulnerability being exploited actively in the wild?
- Has the vulnerability been exploited in your own environment?
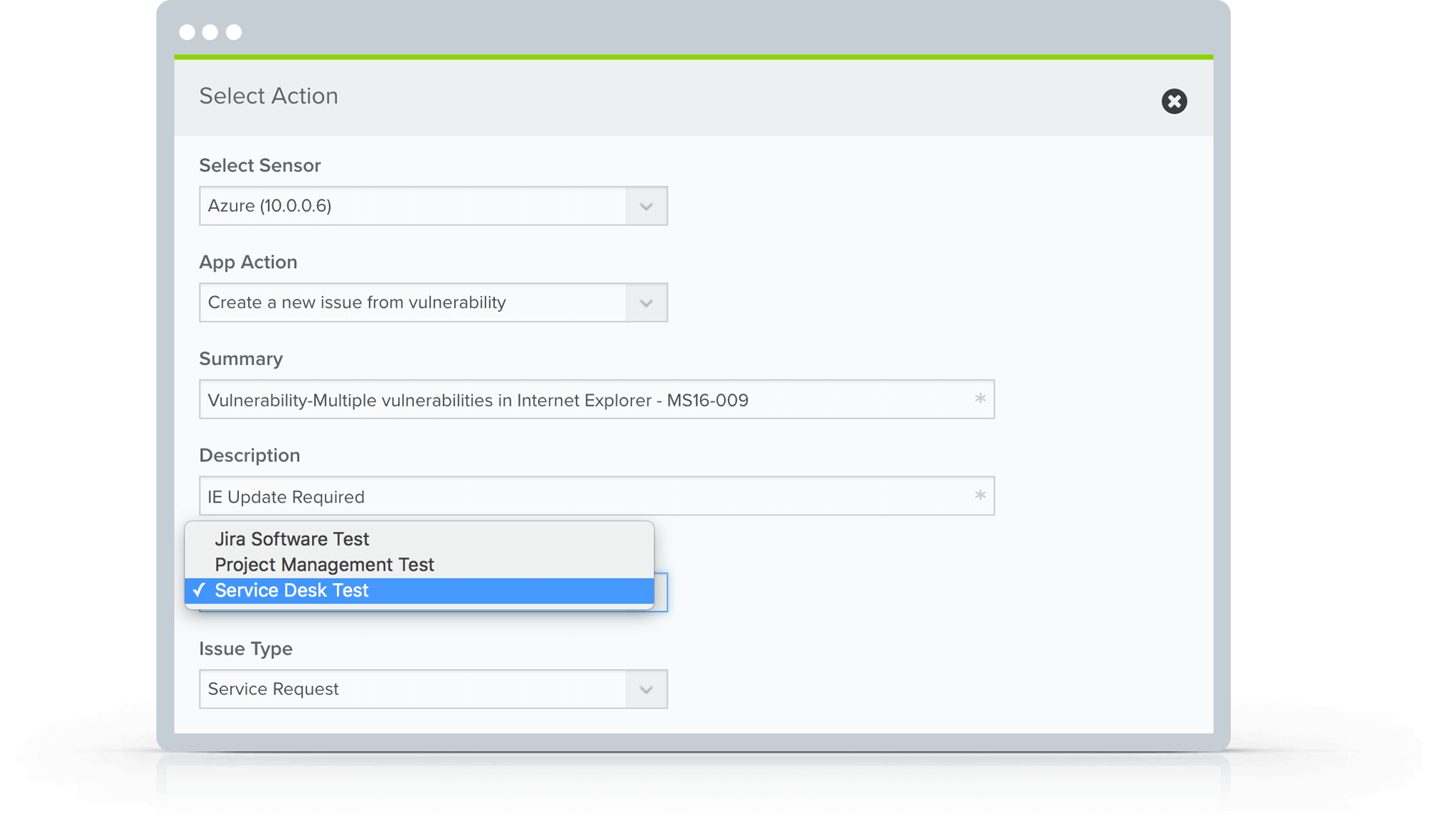
To help you answer these questions, and more, the USM platform delivers information on discovered vulnerabilities, how they affect your environment, and more to help you prioritize and accelerate your response. USM incorporates essential security capabilities – asset discovery, vulnerability assessment, intrusion detection, behavioral monitoring, SIEM event correlation, and log management – to help you understand your security posture and risk.
Identify Which Vulnerabilities Present the Greatest Risk
USM presents the vulnerabilities discovered alongside the software, services, and more of the affected assets. An interactive dashboard shows your most vulnerable assets, vulnerabilities by asset group, a view into the mix of vulnerabilities by their severity (high, medium, and low).
Review Vulnerability History and Patch Information
The USM platform provides details on the history of a vulnerability against each asset, helping identify when the asset first became available, and if an action re-introduced the vulnerability. In addition, information on available patches is provided, saving you from having to research the fixes needed to remediate the risk.
Unified Security Visibility of Assets, Events, and Vulnerabilities
For every vulnerability discovered by USM, you can drill down to see affected assets, related vulnerabilities, events, and much more from a single consolidated view.