USM Anywhere
Start detecting threats on day one and drive operational efficiency with one unified platform for threat detection, incident response, and compliance management.
Overview
Detect threats anywhere
USM Anywhere centralizes security monitoring of networks and devices in the cloud, on premises, and in remote locations, helping you to detect threats virtually anywhere.
Discover
- Network asset discovery
- Software & services discovery
- AWS asset discovery
- Azure asset discovery
- Google Cloud Platform asset discovery
Analyze
- SIEM event correlation, auto-prioritized alarms
- User activity monitoring
- Up to 90-days of online, searchable events
Detect
- Cloud intrusion detection (AWS, Azure, GCP)
- Network intrusion detection (NIDS)
- Host intrusion detection (HIDS)
- Endpoint Detection and Response (EDR)


Respond
- Forensics querying
- Automate & orchestrate response
- Notifications and ticketing
Assess
- Vulnerability scanning
- Cloud infrastructure assessment
- User & asset configuration
- Dark web monitoring
Report
- Pre-built compliance reporting templates
- Pre-built event reporting templates
- Customizable views and dashboards
- Log storage
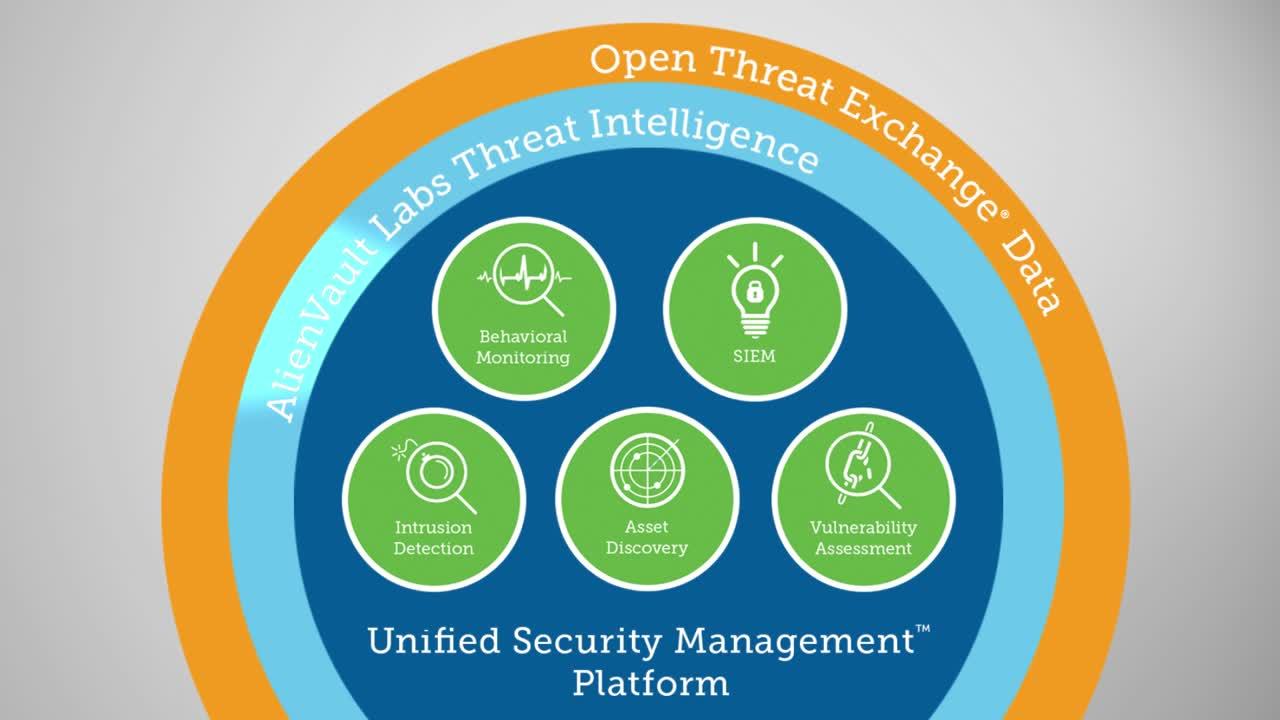
How it works
Focus on actual threats, starting on day one

Smart, automated data collection & analysis
USM Anywhere automatically collects and analyzes data across your attack surface, helping you to quickly gain centralized security visibility without the complexity of multiple disparate security technologies.
Automated threat detection powered by Alien Labs
With threat intelligence provided by Alien Labs, USM Anywhere is updated automatically to stay on top of evolving and emerging threats, so your team can focus on responding to alerts.
Incident response orchestration with AlienApps
USM Anywhere supports a growing ecosystem of AlienApps, enabling you to orchestrate and automate actions towards other security technologies so you can respond to incidents quickly and easily.
AlienApps
Orchestrate and automate your security with AlienApps!
USM Anywhere is a highly extensible platform that leverages AlienApps— modular software components tightly integrated into the USM Anywhere platform that extend, orchestrate, and automate functionality between the built-in security controls in USM Anywhere and other third-party security and productivity tools. With AlienApps, you can:
- Collect critical data from your on-premises and cloud infrastructure as well as cloud services
- Enrich your data and analyze it using the latest AlienVault Threat Intelligence
- Orchestrate and automate your incident investigation and response activities
- Gain new security capabilities as new AlienApps are introduced into USM Anywhere as the threat landscape evolves

Pricing
Essentials
$1075
starting at per month
Ideal for small IT teams looking to set up a security & compliance program quickly, easily, and affordably.
Standard
$1695
starting at per month
Ideal for IT security teams looking to gain efficiency through security orchestration, automation, and deeper security analysis.
Premium
$2595
starting at per month
Ideal for IT security teams looking to meet specific PCI DSS audit requirements.
Compliance
Our Cybersecurity makes compliance a top priority

We make compliance a top priority for your organization and for ours. We have adopted the NIST Cybersecurity Framework (CSF), aligning our security controls and processes with industry-proven security best practices. We use our own USM platform to demonstrate and maintain compliance, working with third-party auditors to regularly test our systems, controls, and processes.
Related products
Managed Threat Detection and Response
24X7 security monitoring
Threat Detection and Response for Government
Reduce risk and protect your data with our FedRAMP Moderate authorized USM platform.
USM Anywhere Advisors
Reduce the burden on your team with reactive security support to help with day-to-day security operations.
Resources
Request info
We're here to help! Complete the form and we will be in touch soon.