Cloud‑based intrusion detection system 〈IDS〉
Detect the latest threats to your cloud environments.
Benefits
Get intrusion detection for cloud and on‑premises with USM Anywhere
A cloud-based intrusion detection system (IDS) is essential for companies migrating workloads and services to public cloud infrastructure like Amazon Web Services (AWS) and Microsoft® Azure.
That’s because cloud environments pose a unique security challenge. While you must monitor for threats and intrusions in the cloud as you do your on‑premises infrastructure, traditional IDS can’t give you full visibility into your cloud environments. Yet, having to purchase and manage a point security solution just for cloud-based intrusion detection can consume time, budget, and resources.
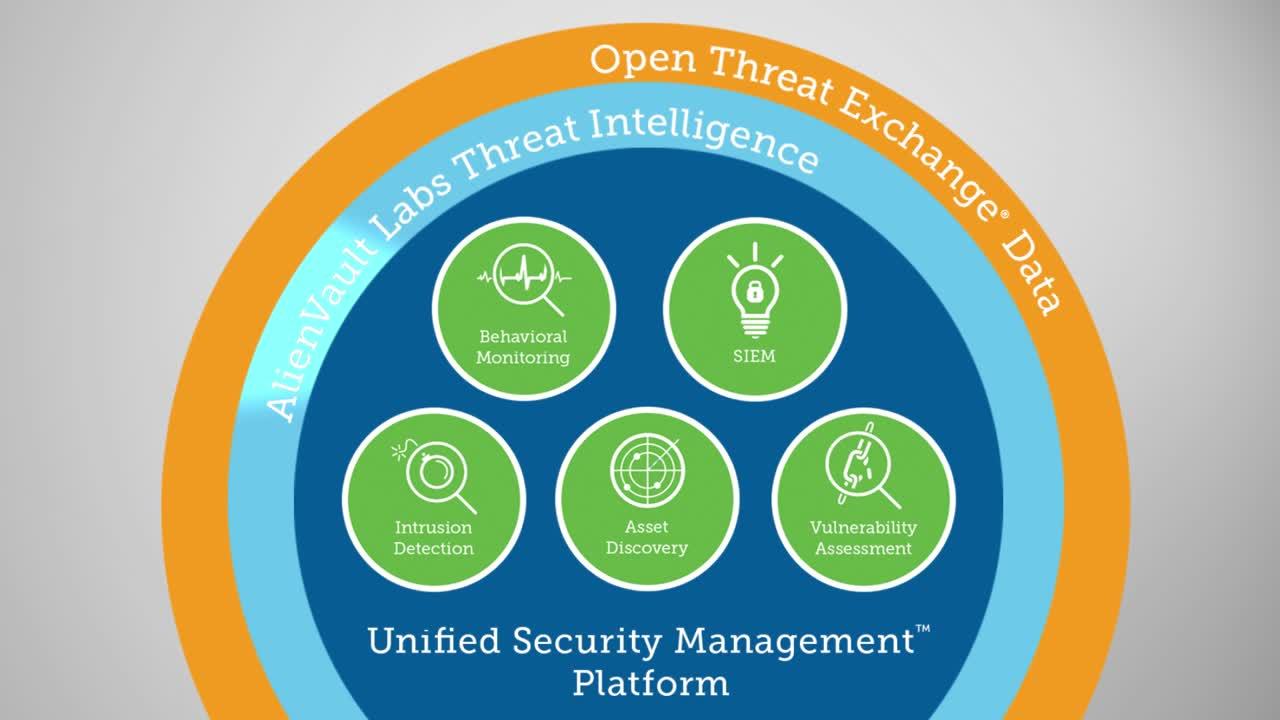
USM Anywhere™ includes native cloud IDS capabilities, offering one platform for intrusion detection, asset discovery, vulnerability assessment, SIEM, log management, and behavioral monitoring for all your cloud and on‑premises infrastructure. By combining these essential security capabilities for cloud and on‑premises onto a single platform, USM Anywhere saves you time and money compared to deploying traditional security solutions.
Deploy one unified solution for security and compliance
USM Anywhere covers network IDS, host-based IDS and cloud-based IDS and offers multiple essential security and compliance monitoring capabilities.
Detect threats across your critical infrastructure
Natively monitor AWS and Azure cloud infrastructure, Microsoft Office 365 and G Suite cloud applications and on‑premises physical environments.
Respond to threats faster with automated incident response
Reduce time to detection (TTD) and time to response (TTR) with automation and push incident response actions to third-party security tools.
Let our security research team do the heavy lifting for you
Receive curated threat intelligence updates from the AT&T Alien Labs security research team - built directly into your USM Anywhere deployment.
Deploy one unified solution for security and compliance
With USM Anywhere’s native cloud-based intrusion detection system (IDS), you can detect threats to your cloud infrastructure from the same console as the rest of your security monitoring needs. By reducing the number of solutions you need to manage, you can free up time and resources for other critical priorities.
Unlike other cloud security solutions, USM Anywhere provides cloud IDS as part of a unified platform that delivers multiple essential security and compliance monitoring capabilities in one cost-effective package:
Asset Discovery
Easily create an inventory of the critical assets you need to monitor across all your environments.
Vulnerability Assessment
Schedule automated internal vulnerability scans to identify and patch vulnerabilities before they’re exploited.
Intrusion Detection
USM Anywhere delivers cloud-based IDS, network-based IDS, and host-based IDS to detect threats across the breadth of your infrastructure.
Behavioral monitoring
Identify patterns of anomalous or suspicious user activity and traffic that can affect your organization’s security posture.
SIEM and log management
Analyze, search, and store event log data to detect threats and anomalies and to prepare for compliance readiness.
By unifying these capabilities in one easy-to-use solution, USM Anywhere helps you conserve time and resources without sacrificing your organization’s security.
Built with resource-constrained teams in mind, USM Anywhere also ensures that your security plan stays up-to-date—without requiring you to devote time to researching emerging threats. Instead, the AT&T Alien Labs Security Research Team continuously builds threat intelligence updates into your USM deployment so you’re always ready to detect the latest threats.
Detect threats across your critical infrastructure
Traditional security monitoring solutions built for on-premises infrastructure have a major blind spot when it comes to the cloud, and attackers know it. Cloud service providers secure the underlying cloud infrastructure, but not any services or applications you deploy in the cloud. Without cloud threat monitoring tools, your organization may be vulnerable to cloud attacks.
USM Anywhere simplifies threat detection by delivering the IDS capabilities you need to detect threats both in the cloud and on-premises, from a single solution.
With USM Anywhere’s purpose-built cloud IDS capabilities, you can count on full security visibility of your cloud environments. Our native cloud sensors are purpose-built for AWS and Azure, and hook directly into the cloud APIs to detect malware, attacks, and other threats that may affect your AWS and Azure environments.
From the same unified solution, you can detect threats to your organization’s cloud IT applications, including Microsoft Office 365 and Google G Suite.
For on-premises threat detection, USM Anywhere delivers both network and host-based intrusion detection (NIDS and HIDS). Network intrusion detection uses signature-based anomaly detection and protocol analysis technologies to detect threats at the network level. With NIDS, you can catch the latest attacks, policy violations, and other exposures affecting your on-premises systems and devices.
Host-based intrusion detection (HIDS) gives you security visibility at the application layer. With HIDS, you can track user access and activity to detect security exposures such as changes to configuration files.
Respond to threats faster with automated incident response
Built with resource-constrained teams in mind, USM Anywhere provides the capabilities you need for faster, more efficient incident detection and response.
USM Anywhere integrates built-in intrusion detection with security orchestration capabilities, enabling you to respond quickly to threats affecting your cloud and on-premises environments. Alarms are prioritized automatically to help you identify on the most urgent threats to work on first, and you can also receive notifications via email or Amazon SNS.
USM Anywhere enables you to respond to threats swiftly and effectively. For example, you can define an action that disables networking on a machine if ransomware is detected, preventing the attack from propagating while you investigate.
You can also execute response actions towards third-party security tools like Cisco Umbrella and Palo Alto Networks next-generation firewalls directly from USM Anywhere. That’s because USM Anywhere delivers pre-built integrations known as AlienApps™ that connect with other essential security and IT products. AlienApps enable you to orchestrate your threat detection and incident response activities across your IT ecosystem—all from a single pane of glass.