DevOps security solutions
Bring security into your DevOps practice with AlienVault USM.
AlienVault USM Delivers Continuous Security Monitoring for DevSecOps Teams
DevSecOps (or DevOps security) is an approach to software development and delivery that addresses security and operations concerns throughout the build and test phases, rather than waiting until the software is in production. A robust DevSecOps practice has the potential to enable more securely built software products and SaaS environments without slowing down innovation or continuous delivery.
However, traditional security tools often lack the modern features and cloud-readiness that DevOps teams rely on to automate, integrate, and otherwise streamline their continuous integration continuous delivery (CICD) pipeline, which can lead to bottlenecks, information silos, security blind spots, and other inefficiencies. Similarly, tools built for DevOps do not typically include the security testing and monitoring capabilities needed to ensure an application’s security.
AlienVault® Unified Security Management® (USM) is different. Unlike any other security monitoring and compliance solution, AlienVault USM delivers automated threat detection, incident response, and compliance management across cloud, on-premises, and hybrid environments—all in a unified, affordable SaaS solution. With it, DevSecOps teams can accelerate their security and compliance efforts without the overhead of a traditional approach to security.
Whereas traditional SIEMs and security products can take weeks, if not months, to install, setup, and integrate into your environment, AlienVault USM enables you to go from installation to security insights within minutes.
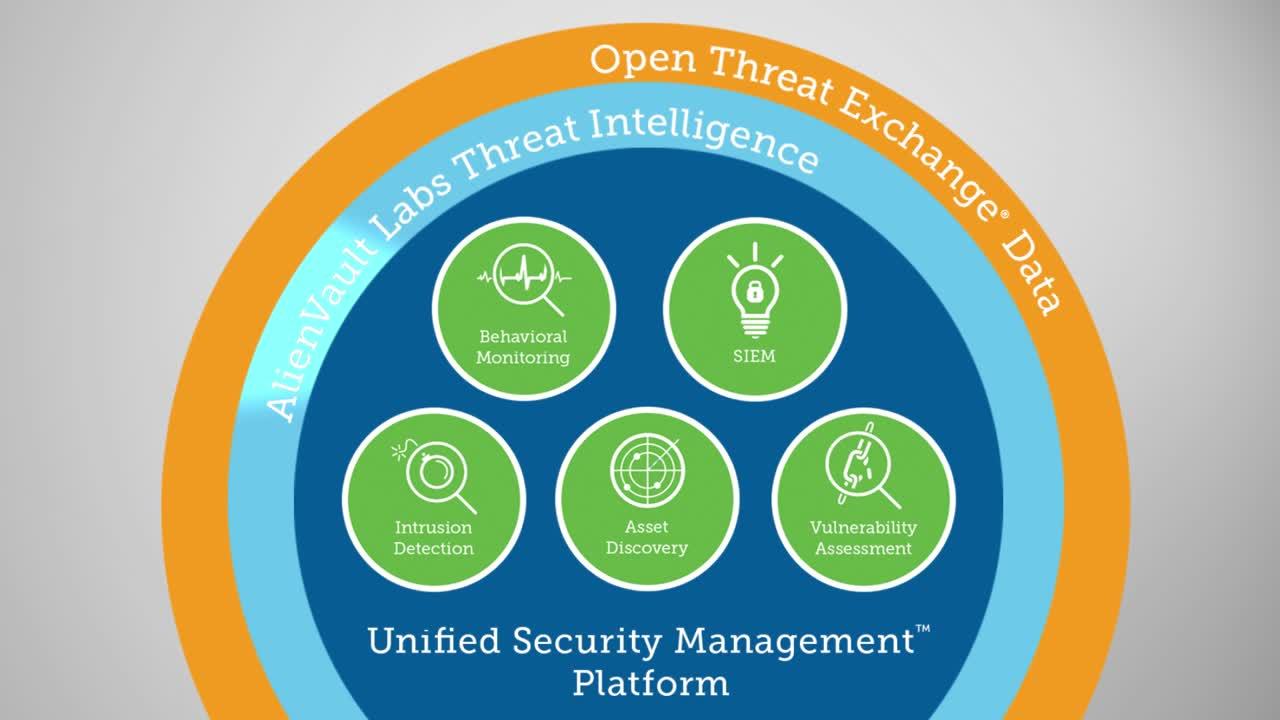
AlienVault USM equips DevOps teams with the essential security capabilities needed to accelerate DevSecOps without slowing down continuous delivery, including asset discovery, vulnerability assessment, intrusion detection, SIEM, log management, and more. With AlienVault USM, you can:
- Streamline security monitoring across all environments. Reduce security and compliance bottlenecks by streamlining security monitoring across your build, test, and production environments, whether on premises or in the cloud. Learn more
- Automate threat detection and incident response. Protect your continuous delivery pipeline with real-time threat detection, incident response automation, and security orchestration with DevOps tools like Jira, PagerDuty, and others. Learn more
- Ease compliance requirements. Leverage pre-built and customizable compliance reports to demonstrate continuous compliance without spreadsheets. Learn more
- Always use the latest threat intelligence. AlienVault USM receives continuous threat intelligence updates from AlienVault Labs and the OTX, keeping you up to date with real-world threats with zero effort. Learn more
Streamline Security Monitoring across All Environments
The “shift security left” ethos of DevSecOps spans the entire technology stack, including the critical infrastructure in your development and testing (DevTest), staging, and production environments. By injecting security monitoring into your build pipeline, you can ease security and compliance requirements, identify critical vulnerabilities and other security flaws earlier, and detect malicious actors trying to insert malware in your builds or stealing your intellectual property.
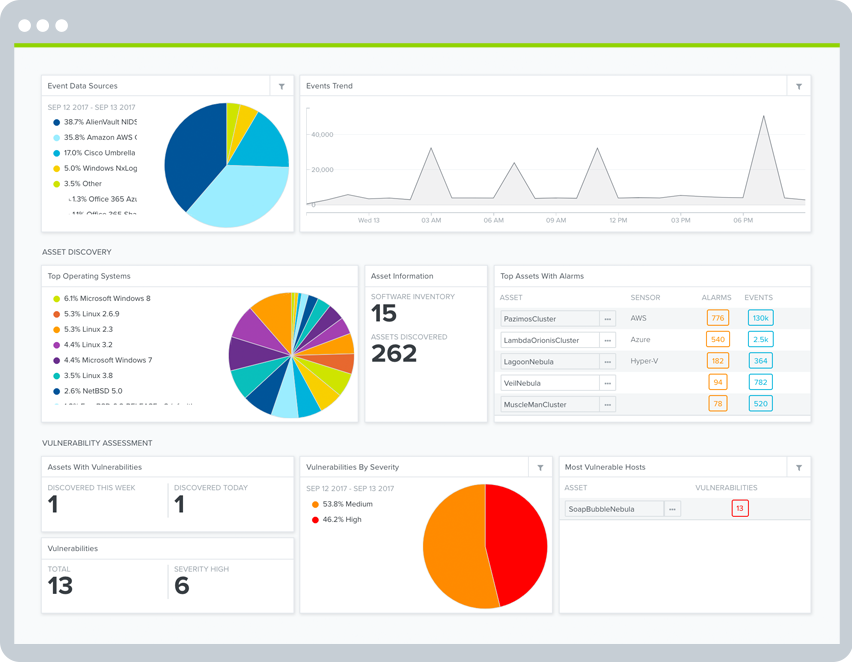
With AlienVault USM, you can centralize security monitoring and compliance management across all of your critical infrastructure and environments, including AWS and Azure cloud accounts, physical and virtualized on-premises infrastructure, and cloud applications.
With AlienVault USM monitoring across your entire build to production pipeline, you can maintain continuous security visibility as you promote builds, giving you greater predictability as to how the infrastructure security will operate in production as well as a more streamlined compliance management. In addition, you can accelerate your development cycles with earlier detection of critical vulnerabilities, cloud configuration issues, and other security issues that could impact delivery.
AlienVault USM combines multiple essential security capabilities into one unified solution, so you can centrally monitor all assets, vulnerabilities, and threats from a single pane of glass. It includes the following essential security capabilities:
- Asset Discovery — Automatically discovers and groups assets in your environments, including dynamic AWS and Azure instances and services.
- Vulnerability Assessment — Authenticated and unauthenticated vulnerability scanning technologies continually identify and prioritize the vulnerabilities on your critical assets.
- Intrusion Detection — Our multi-layered approach to IDS includes network, host, and native cloud intrusion detection capabilities for advanced threat detection.
- Behavioral Monitoring — Monitors user and administrator activities on AWS (CloudTrail, S3, ELB, VPC Flow logs) and Azure (Azure Monitor, Azure Diagnostics Logs) for anomalous activities.
- SIEM and Log Management — Event correlation prioritizes security events and alerts you to emerging threats in real time. Includes secure raw log storage for the life of the active USM Anywhere subscription.
Automate Threat Detection and Incident Response
DevOps is built on Agile and Lean principles, with a focus on automation that enables rapid application development and continuous enhancement to meet new requirements and accelerate business objectives. Similarly, DevSecOps security principles call for automation in security monitoring tools in order to keep pace with today’s dynamically changing IT environments and emerging threats. Unfortunately, legacy SIEM solutions often lack the extensibility and adaptability that DevSecOps teams need achieve continuous security monitoring and compliance.
In contrast, AlienVault USM delivers advanced security automation, helping DevSecOps teams to achieve faster, more efficient threat detection and incident response. For example, when AlienVault USM detects critical vulnerabilities and threats in your environment, it uses automated prioritization processes, so that you know which vulnerabilities and threats to focus on first. AlienVault USM weighs factors like how recent the threat is, how valuable the vulnerable assets are to your organization, and what data source the event data came from.
AlienVault USM also enables you to orchestrate and automate security incident investigation and response activities by defining security orchestration rules. For example, if AlienVault USM detects evidence of malware on one of your assets, you can create an orchestration rule to fetch additional data for fast investigation. When investigating a potentially compromised server, you might want to see what connections are set up, who has logged onto the machine, what processes and services are running on the machine, or your own custom query results. You might also want to orchestrate response actions, such as disabling networking on the device or otherwise isolating it while you remediate.
Extend Security Orchestration with AlienApps
AlienApps™ are modular components that extend the threat detection and incident response capabilities of AlienVault USM to third-party security tools and cloud applications. AlienApps interact with security tools like Palo Alto Networks, Cisco Umbrella, and Carbon Black, as well as with cloud apps, including Office 365, G Suite, and Okta, for centralized threat detection and incident response.
With AlienApps, the USM platform serves as a powerful security orchestration and automation platform. AlienApps collect and enrich data from these sources and enable AlienVault USM to analyze it against the latest AlienVault Threat Intelligence. When threats are detected, you can orchestrate and automate investigation and response activities directly from within the USM platform. For example, if USM Anywhere detects a malicious IP, it can notify your Palo Alto Networks firewall to block the IP address.
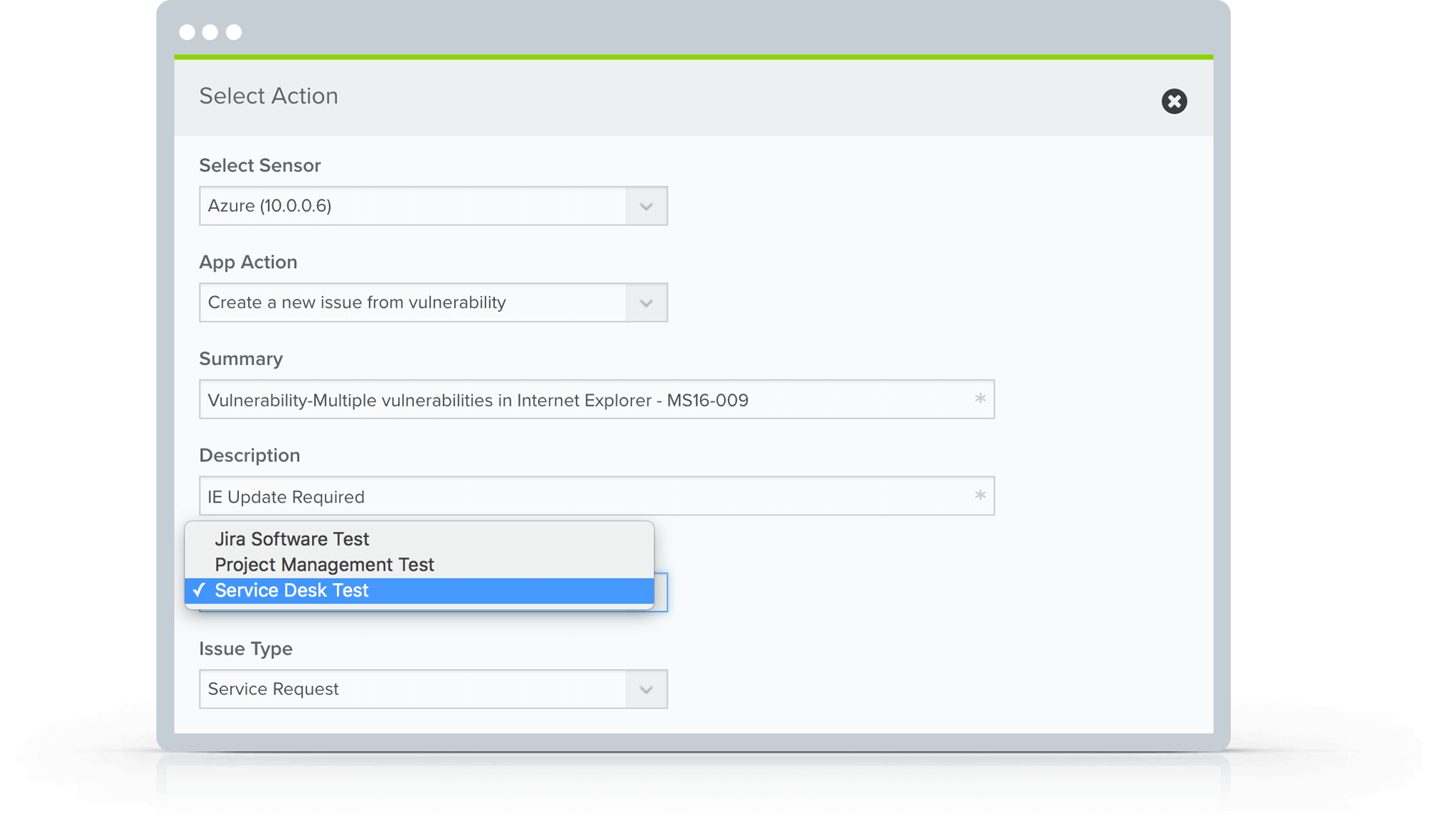
Automate Incident Response Workflows in Jira and ServiceNow
With AlienVault USM, you can automate incident response workflows with third-party ticketing software, including Jira and ServiceNow. As vulnerabilities and incidents arise, you can easily open and track Jira or ServiceNow issues directly within the USM platform, making it easy, fast, and efficient to monitor workflow, even across multiple security, IT, and development teams.
Send Real-time Notifications to PagerDuty, Slack, and Datadog
AlienVault USM supports direct integration with Slack, Datadog, and PagerDuty, as well as with Amazon Simple Notification Service (SNS) to send e-mail and SMS notifications, and for custom integrations with other messaging services. With this direct integration, you can create orchestration rules in AlienVault USM that send notifications to any of these channels in response to an alarm or event. That way, your DevSecOps team can stay on top of security issues without having to introduce yet another communication tool.
Ease Compliance Requirements
Many compliance standards have explicit requirements for developing software in secure and controlled environments as well as scanning those environments for vulnerabilities and remediating any vulnerabilities within a certain amount of time. And for good reason. If you build vulnerable software or run it in insecure environments, you could risk losing users’ personal information or credit card data, resulting in hefty fines.
However, in the eyes of many development teams, compliance too often looks like a checklists and paperwork, spreadsheets of vulnerabilities tossed over the fence right before deployment, and requests to manually compile lists of assets for auditors and compliance officers. In short, compliance is often seen as the antithesis of DevOps. But, it doesn’t have to be. Given that security and compliance requirements are increasingly becoming the responsibility of DevSecOps teams, AlienVault USM provides an easier, more automated, and affordable approach to compliance management.
AlienVault USM simplifies and accelerates compliance management for DevSecOps teams in multiple ways:
- Asset Discovery and Vulnerability Assessment continuously scans your environment to dynamically discover all of your cloud and on-premises assets. Internal vulnerability scans run regularly, and you can run an on-demand vulnerability scan of any asset group, for example a PCI CDE asset group.
- Log Collection, Analysis, & Event Correlation collects log data from your environment. The data is normalized, timestamped, and immediately made available to search on and run reports on, up to 90 days of online searchable events.
- Pre-built Compliance Reports in our library of “audit-ready” reports including PCI DSS, HIPAA, and NIST CSF help you to accelerate your compliance process and be ready faster for your next audit.
- Compliance-Ready Log Storage securely keeps your log data in the secure cloud. Up to your most recent 90 days of events are searchable in the USM platform, and logs are stored in cold storage for the life of the active USM Anywhere subscription.
- AlienVault is Certified Compliant to widely-accepted compliance standards, including PCI DSS, HIPAA, and SOC 2, so you can rely on our secure log storage as you pursue your own certification efforts.
Always Use the Latest Threat Intelligence
DevOps engineers must wear many hats: IT manager, developer, cloud architect, and evangelist, to name a few. Adding security researcher to that list could quickly consume all of your valuable DevOps resources. While it’s critical for DevSecOps teams to be security-minded, it’s not practical for them to scour the global threat landscape daily, hunting for the latest attack vectors.
Luckily, the AlienVault Labs Security Research Team does it for you. This team uses human and machine intelligence to analyze and validate threat artifacts, including threat data contributed by the global OTX community, and updates the AlienVault USM platform continuously and automatically with actionable threat intelligence updates. So, you always stay up to date with the emerging threat landscape with zero effort on your part.