In recent weeks, there have been some high-profile reports about Mac malware, most notably OSX/Dok and OSX.Proton.B. Dok malware made headlines due to its unique ability to intercept all web traffic, while Proton.B gained fame when attackers replaced legitimate versions of HandBrake with an infected version on the vendor’s download site. Another lower profile piece of Mac malware making the rounds is Mac.Backdoor.Systemd.1.
Figure 1: Systemd pretending to be corrupted and un-runnable.
There have been no public reports as to who is behind these attacks and only little information about their targets. OSX/Dok is reported to have targeted European victims, while users of HandBrake were the victims of Proton.B. One corporate victim of Proton.B was Panic, Inc. which had its source code stolen and received a ransom demand from the attackers.
Each of these malware variants is designed to take advantage of Macs, but analysis shows that they are actually drastically different from each other, showing just how diverse the Mac malware space has grown. Let’s dive into some of the technical details (but not too technical :wink: of each piece of malware to learn more about what they do and how they work.
| OSX/Dok | OSX.Proton.B | Mac.BackDoor.System.1 | |
| Functionality |
HTTP(S) proxy |
Credential theft (potentially other RAT functionality) |
Backdoor/RAT |
| Language |
Objective-C (with heavy use of shell commands) |
Objective-C (with heavy use of shell commands) |
C++ (with a handful of shell commands) |
| Persistence |
Launch Agent |
Launch Agent |
Launch Agent Launch Daemon Startup Item Uses chflags to make files read-only |
| Distribution |
Phishing emails |
Compromised software download |
(presumably) Phishing |
| Anti-Analysis |
None |
Anti-debugger (PT_DENY_ATTACH) Closes Terminal and Wireshark Windows |
None |
| Binary Obfuscation |
Newer variants are packed with UPX |
Password protected zip archive Encrypted configuration file |
Encrypted configuration file XOR encrypted strings in binary |
| Detection Avoidance |
Signed App bundle Installs trusted root certificate Modifies sudo settings to prevent prompting |
Checks for security software Infected legitimate software Use of “hidden” dot files |
Uses chflags to hide files from UI Use of “hidden” dot files |
| C2 |
MiTM proxy (no separate C2) |
HTTPS |
Custom 3DES |
Functionality
Dok is very basic in its functionality – it reconfigures a system to proxy web traffic through a malicious host. It does this by installing Tor and changing web proxy settings to hijack web traffic in order to steal credentials or even alter content. There is no need for the victim to communicate with a command and control server since the malicious proxy server already has access to the information its trying to steal.
Proton.B might be a slimmed down version of Proton.A which contains a full-featured suite of RAT functionalities. However, while Proton.B is reported to have only basic credential stealing capabilities, it does have the capability to run arbitrary commands from its configuration file. The decrypted configuration file also shows hints of other capabilities, such as grabbing screenshots and SSH tunneling. Proton.B is also able to steal credentials by collecting them from keychains, password vaults, and web browsers. The credentials are then exfiltrated over HTTPS.
Systemd.1 is a basic backdoor/RAT that waits for commands from a command and control server. This backdoor is able to either listen on a network socket for an incoming C&C connection or make its own connection to a C&C. Commands from the C&C allow attackers to do things like: run arbitrary commands, perform file system operations, update the backdoor software, update the C&C server, and install plugins.
Language and Distribution
Windows malware often comes in a variety of formats – ranging from office documents, script files, executables, or malicious PDFs just to name a few. In contrast, Mac malware tends to have much less variation and most often shows up as a Mach-O executable, zipped app bundle, or DMG file. There has been a recent case of malicious Office documents targeting Macs and back in 2012 AlienVault also reported on Office documents targeting Macs, but those are exceptions to the norm.
Dok is distributed as a zipped app bundle written in Objective-C, but also uses a shell script to perform critical functionality. The zipped app bundle is typically sent as an attachment to a phishing email and requires the victim to execute the application.
Proton.B is also written in Objective-C, but the malicious code is distributed with the popular video transcoding tool HandBrake. Proton.B uses HandBrake to bootstrap loading of its own code and tricks victims into entering in their password by presenting a fake authentication prompt.
Systemd.1 is different from Dok and Proton in that it is written in C++. We’re not sure of its initial infection vector, but we can posit that it is via phishing since the samples[1] in VirusTotal are often named “Confidential_Data”. It is possible that the Systemd.1 Mach-O is distributed along with an app bundle, but we have not discovered that link yet. (As a side note, we’ve previously looked at another piece of C++ Mac malware, OceanLotus, and Systemd.1 does some similar things like decrypting XOR encrypted strings in __mod_init, however, Systemd.1 has fewer features.)
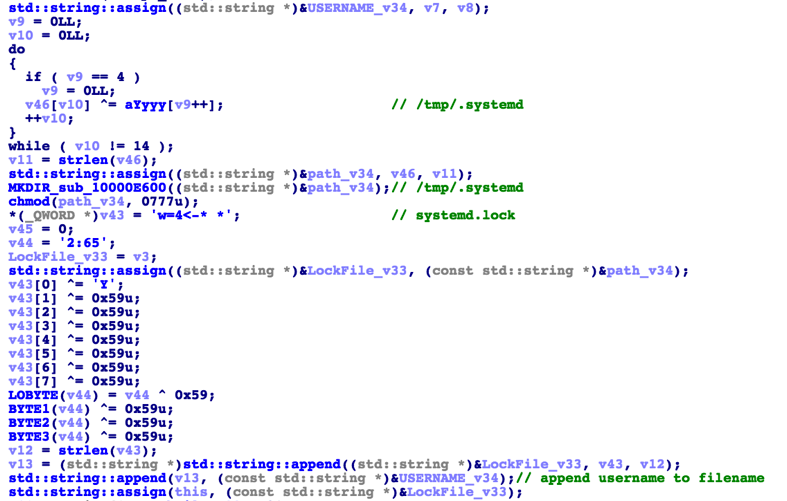
Figure 2. Systemd XOR decrypting strings
Persistence
Even though there are several ways that malware can persist on Macs, we find that most choose to use launch agents and launch daemons. Here, Dok and Proton use launch agents while Systemd.1 uses both agent and daemon. To make things extra sticky, Systemd.1 also uses the deprecated Startup Items feature in OSX and drops files in /Library/StartItems.
/Library/StartupItems/sysetmd/StartupParameters.plist will contain the following text
|
{ Description = "Start systemd"; Provides = ("system"); Requires = ("Network"); OrderPreference = "None"; } |
And /Library/StartupItems/sysetmd/sysetmd will look like:
|
#!/bin/sh . /etc/rc.common StartService (){ ConsoleMessage "Start system Service" /Library/sysetmd d } StopService (){ return 0 } RestartService (){ return 0 } RunService "$1" |
Systemd.1 also makes it slightly harder to remove the malware by using the “chflags” command to make files read-only.
Anti-Analysis, Binary Obfuscation and Detection Avoidance
Initial samples of Dok did not have any obfuscation or anti-analysis code, however, newer variants are being packed with UPX. In order to suppress security prompts from the operating system, Dok was cryptographically signed by a valid developer. Furthermore, Dok installs a malicious trusted root certificate so that web browsers won’t alert users that their HTTPS traffic is being intercepted by a proxy.
Figure 3. Dok signed with a legitimate certificate
Proton.B attempts to thwart analysis by preventing debuggers from attaching to it (though this can be easily bypassed). It also kills Terminal and Wireshark processes – both of which would be used by someone who wanted to analyze the malware. As previously mentioned, Proton.B was distributed with a modified version of HandBrake. Modified versions extract the core Proton.B binary from a password protected (encrypted) zip file. Although the Proton.B executable itself is not obfuscated, its configuration file is encrypted. Once executed, Proton.B checks for the presence of popular security software Little Snitch, Radio Silence and HandsOff – if present, it stops running. Popular in *nix-based malware, Proton.B also uses “hidden” dot files to make it harder to see.
Systemd.1 does not have any anti-debugging measures, but does XOR encrypt several strings in the binary. These strings are decrypted at runtime along with a 3DES encrypted configuration file. Systemd.1 also uses hidden dot files and directories, but goes one step further and hides files with the “chflags hidden” command.
Takeaways
As you can see, these three pieces of malware are distinct from each other in their approaches and illustrate the diversity of Mac malware variants that have surfaced in just the past few weeks. One can only expect the diversity to increase in the future. In particular, we’d expect future Mac malware to utilize more anti-analysis and obfuscation techniques since there is a lot of low hanging fruit on that front.
If you want to find out more about these malware variants, here are some of the pulses we have in our Open Threat Exchange (OTX):
Detection
There are many ways to detect the presence of these and other Mac-based malware variants in your environment. We’ve included some of those methods.
Yara rules
You can use the rules below in any system that supports Yara to detect these Mac-based malware variants.
|
rule mac_bd_systemd { meta: author = "AlienVault Labs" type = "malware" description = "OSX/Proton.B" strings: $c1 = "This file is corrupted and connot be opened" $c2 = "whatismyip.akamai.com" $c3 = ";chflags hidden" $c4 = "%keymod%" $c5 = "* *-<4=w" condition: 3 of ($c*) } rule osx_proton_b { meta: author = "AlienVault Labs" type = "malware" description = "Mac.Backdoor.Systemd.1" strings: $c1 = "%@/%@%@%@%@%@" $c2 = { 2e 00 68 00 61 00 73 00 } //. h a s $c3 = "Network Configuration needs to update DHCP settings. Type your password to allow this." $c4 = "root_password" $c5 = "decryptData:withPassword:error:" $c6 = "-----BEGIN PUBLIC KEY-----" $c7 = "ssh_user" condition: 5 of ($c*) } rule osx_dok |
|
{ meta: author = "AlienVault Labs" type = "malware" description = "OSX/Dok" strings: $c1 = "/usr/local/bin/brew" $c2 = "/usr/local/bin/tor" $c3 = "/usr/local/bin/socat" $c4 = "killall Safari" & $c5 = "killall "Google Chrome"" $c6 = "killall firefox" $c7 = "security add-trusted-cert -d -r trustRoot -k /Library/Keychains/System.keychain %@" condition: all of them } |
Osquery
The osquery project already has some rules for Dok and Proton which you can find here:
For Systemd, you can add the following queries:
|
{ "platform": "darwin", "version": "1.4.5", "queries": { "Systemd_Files": { "query" : "select * from file where path like '/Library/StartupItems/sysetmd/StartupParameters.plist' OR path like '/Library/StartupItems/sysetmd/sysetmd' OR path like '/Library/sysetmd' OR & path like '/Users/%/Library/sysetmd' OR path like '/private/tmp/.systemd/systemd.lock%' OR path like '/private/var/root/.local/.systemd/systemd.uniq%';", "interval" : "3600", "description" : "Mac.BackDoor.Systemd", & "value" : "Artifacts created by this malware" }, "Systemd_Launch": { "query" : "select * from launchd where name like 'com.app%le.sysetmd.plist';", "interval" : "3600", "description" : "SystemD Launch Agent/Daemon", "value" : "Artifact used by this malware" } } } |
Appendix
Hashes for Mac.Backdoor.Systemd.1:
6b379289033c4a17a0233e874003a843cd3c812403378af68ad4c16fe0d9b9c4 37152cfcfb9b33531696624d8d345feb894b5b4edd8af2c63a71e91072abe1ad c549c83577c294cc1323ca94e848389fce25510647ec5212fa2276de081771ca 3f71b6b994eabbc32a63eac14e9abd7b6cd26c37ed0baacbfbe62032c5930a40