A couple of days ago, Adobe issued a security update for Adobe Flash Player that has been detected in the wild targeting specific objectives.
Several spear phishing campaigns have been detected. The mails sent contain a Word document attachment. It contains a reference to a Flash file that is downloaded from a remote server once the document is opened. This Flash file exploits the CVE-2012-0779 vulnerability triggering a shellcode that looks for the payload within the original word document. The payload is decoded using a one byte XOR scheme, dropped on the system and then executed.
Most of the malicious Flash files have low AV detection rates so it is very important to apply the vendor’s patch.
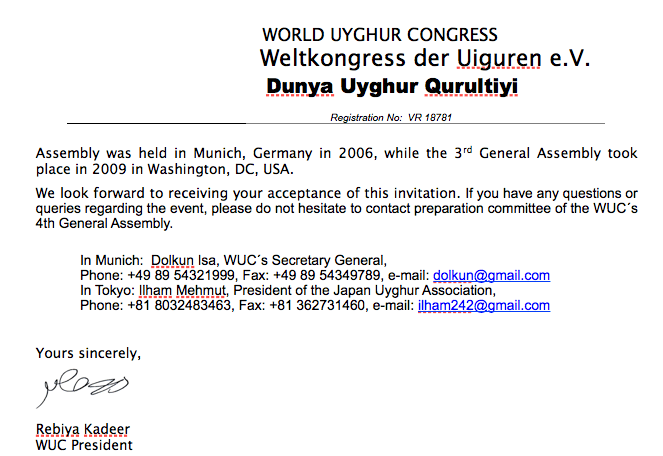
We have seen several documents sent to a wide range of industries as well as Tibet related NGO’s. Some examples are:
Once the victim opens the document, the malicious Flash file is downloaded from a remote server:
In the vast majority of the documents we have analyzed, the malicious files are hosted on hacked websites.
We will release more information as well as IDS signatures to detect some of the payloads we have seen so far.





