AlienVault provides basic file integrity monitoring out of the box with our HIDS agent. Sometimes a more robust and detailed audit trail is required, and with a little configuration up front, AlienVault USM can provide rich monitoring and reporting capability for your sensitive files.
Step 1: Preparing group policy for file auditing
In order to track file system changes on a Microsoft Active Directory Domain, first, you must set a group policy to keep track of file system changes. In the following examples, we will be using the default domain controller policy, as we are tracking changes on a domain controller. Your actual policy may be different, depending on your particular domain configuration.
First, from the Server Manager, open up Group Policy Management, and expand the domain to select the policy you wish to edit:
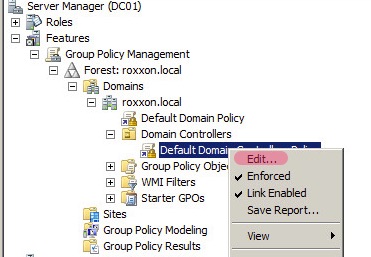
Right click on the policy and choose edit.
The first thing we need to change, is the option to allow the more granular advanced audit policy settings, instead of the general categories that are enabled by default:
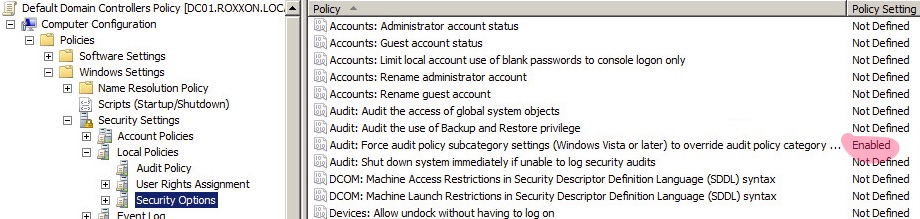
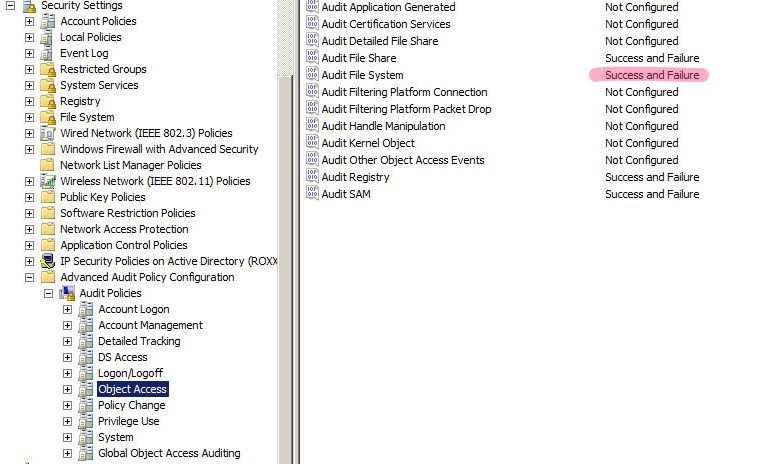
Then, further down in the security settings, locate “Advanced Audit Policy Configuration” and expand it as shown. We are primarily concerned with object auditing in this exercise, but you will need to make sure the other policies, such as account lockout, etc. are correct for your organization. Remember, these advanced policies are now taking precedence.
See the settings in the screenshot. The highlighted setting is the critical item for our integrity monitoring:
OK, now we’ve got the policy set, go ahead and close this out, and verify the Group Policy you just edited is enforced and applied to the domain per your particular configuration.
Step 2: Folder Preparation
In order for the policy to be effective, you need to enable auditing on the directories you want to monitor. You may be tempted to just enable the entire filesystem, and inherit throughout, and you could. This will be extremely detrimental to the operation of the server involved, creating hundreds or thousands of events per minute. It is also useful to consider how often you expect changes to the folder(s) you are auditing. It can get quite noisy.
The following screenshots show how to enable auditing on a particular folder:
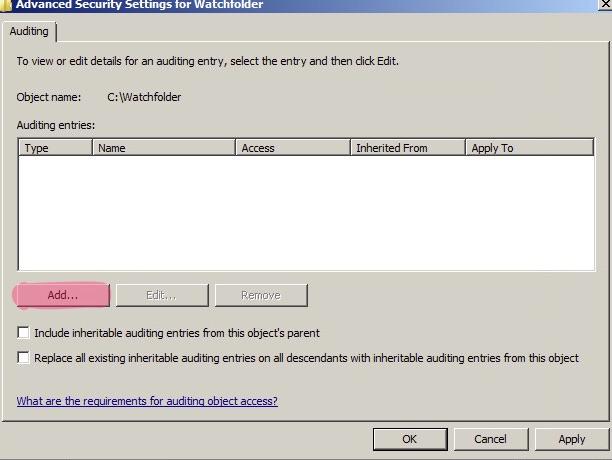
Right-click the folder and choose “Properties” then the”Security” tab. Click “Advanced”, then the “Auditing” tab. By default, the “Auditing entries” section will be blank. Select “Edit”
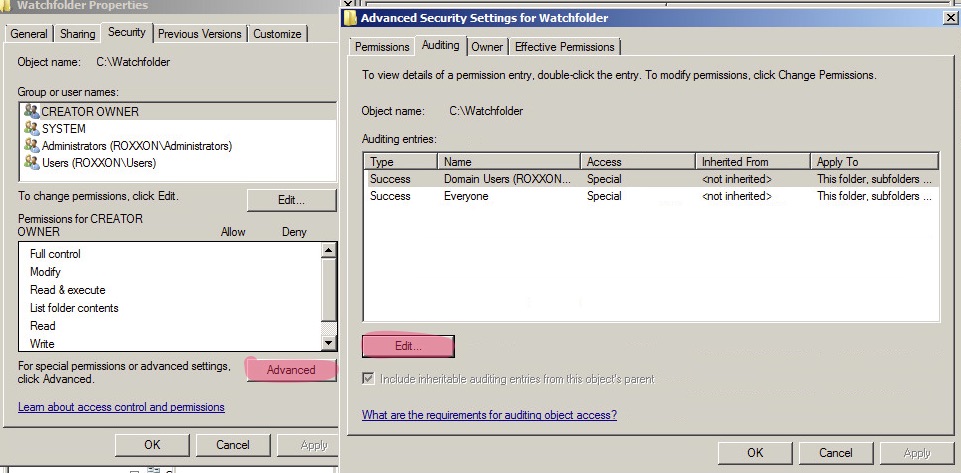
Select “Add:” and select the AD group(s) you wish to be subjected to auditing and click OK.
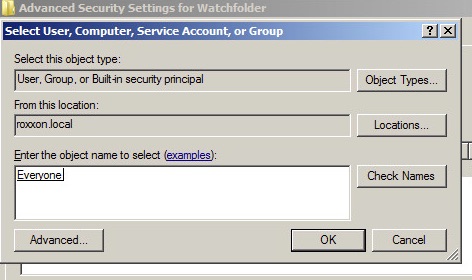
You will then get a dialog box to select the type of auditing you wish to set:
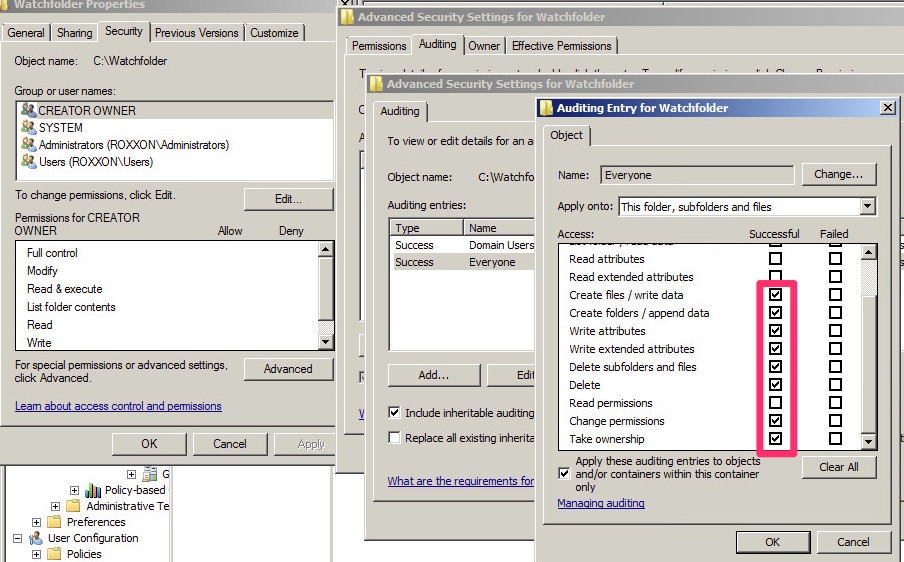
The highlighted items should be selected for effective auditing, but we will be primarily leveraging the Create, Write, Append, and Delete.
Step 3: Testing and Viewing Events
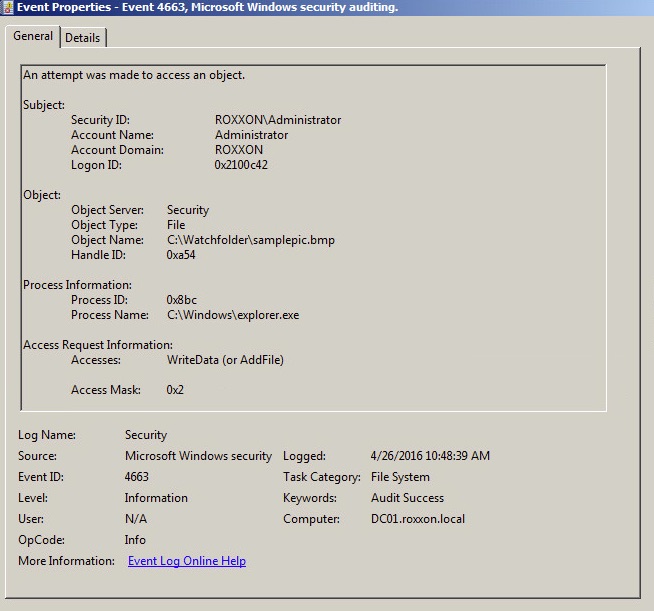
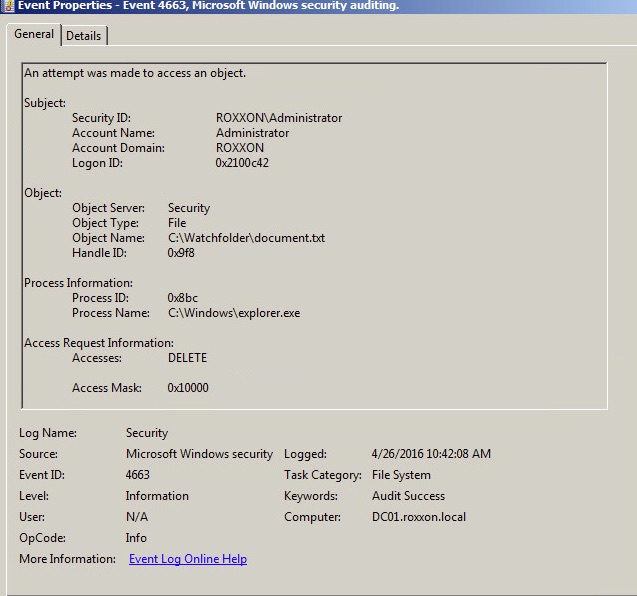
After auditing is set, we should then test to make sure the events are properly generated in Windows Event Viewer. To do this, we should create a file, edit it, move it out of the folder, and back in. This should generate the events in the Event Viewer as shown:
Step 4: Preparing USM
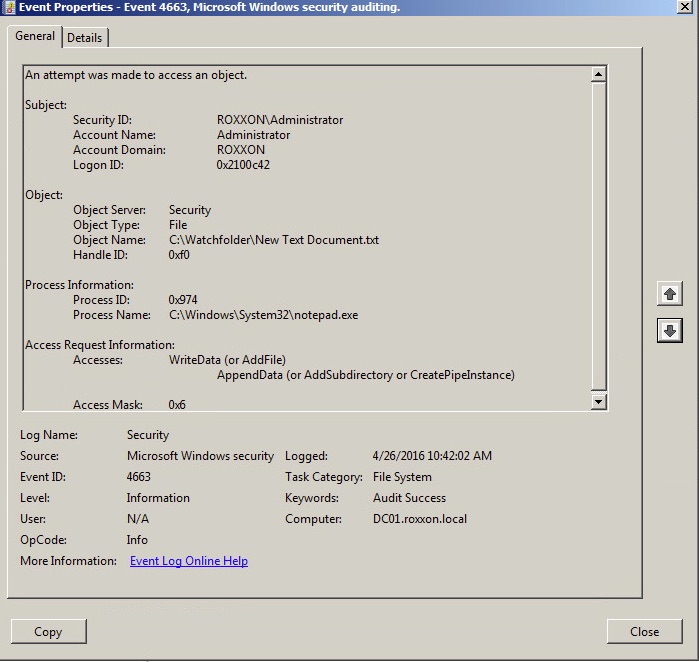
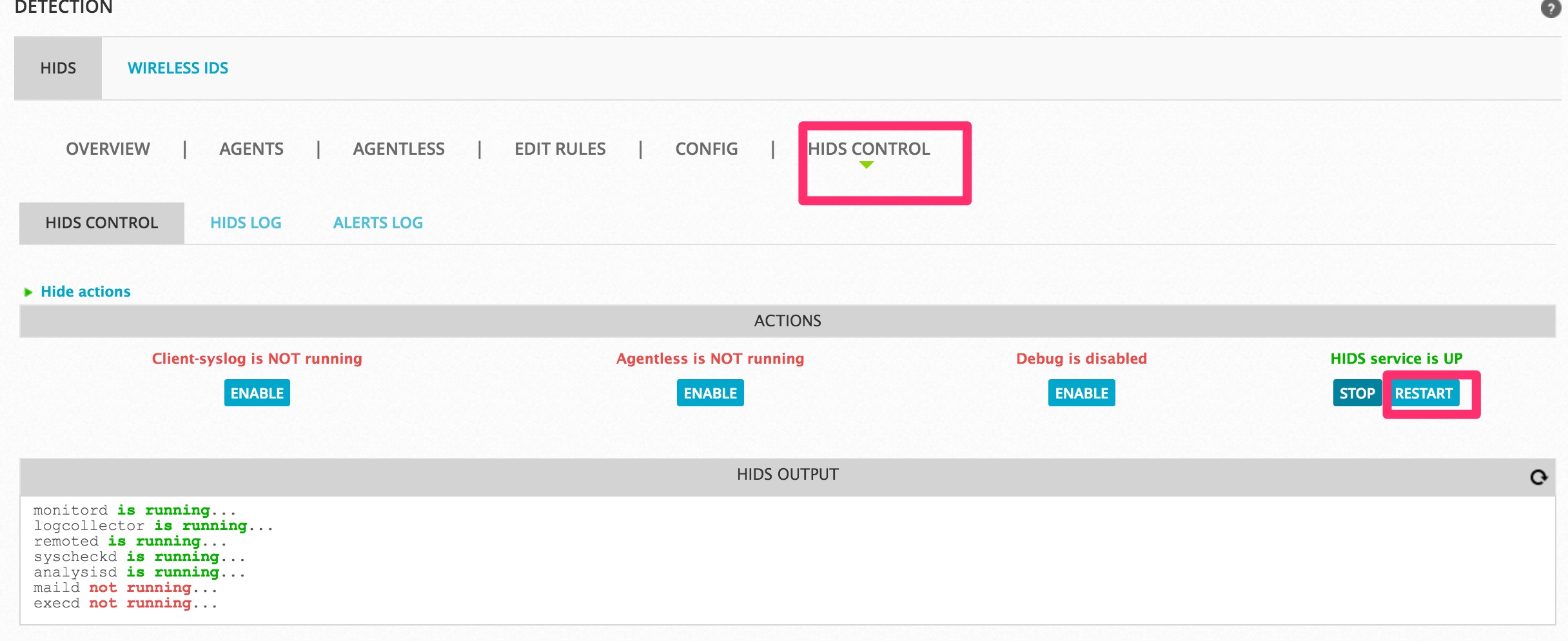
By default, the AlienVault USM has a plugin to parse these events, but the HIDS process needs a small edit first. Release 5.3 will have this fully integrated, but for now, log into the USM and navigate to “Environment” → “Detection” → “Hids” → “Edit Rules”
Make sure you have local_rules.xml selected, and the “Rule Editor” tab selected.
Highlight all the sample text on the right, delete it, preserving any customizations you might have placed there. (by default, there should be just sample stuff - you can delete it.)
Paste the following, and click save:
18104 ^AUDIT_SUCCESS|^success Access Mask: 0x10000$ Windows file deleted. 18104 ^AUDIT_SUCCESS|^success Access Mask: 0x2$ Windows file added. 18104 ^AUDIT_SUCCESS|^success Access Mask: 0x6$ Windows file appended. 18104 ^AUDIT_SUCCESS|^success Access Check: 0x120080 Windows file opened.
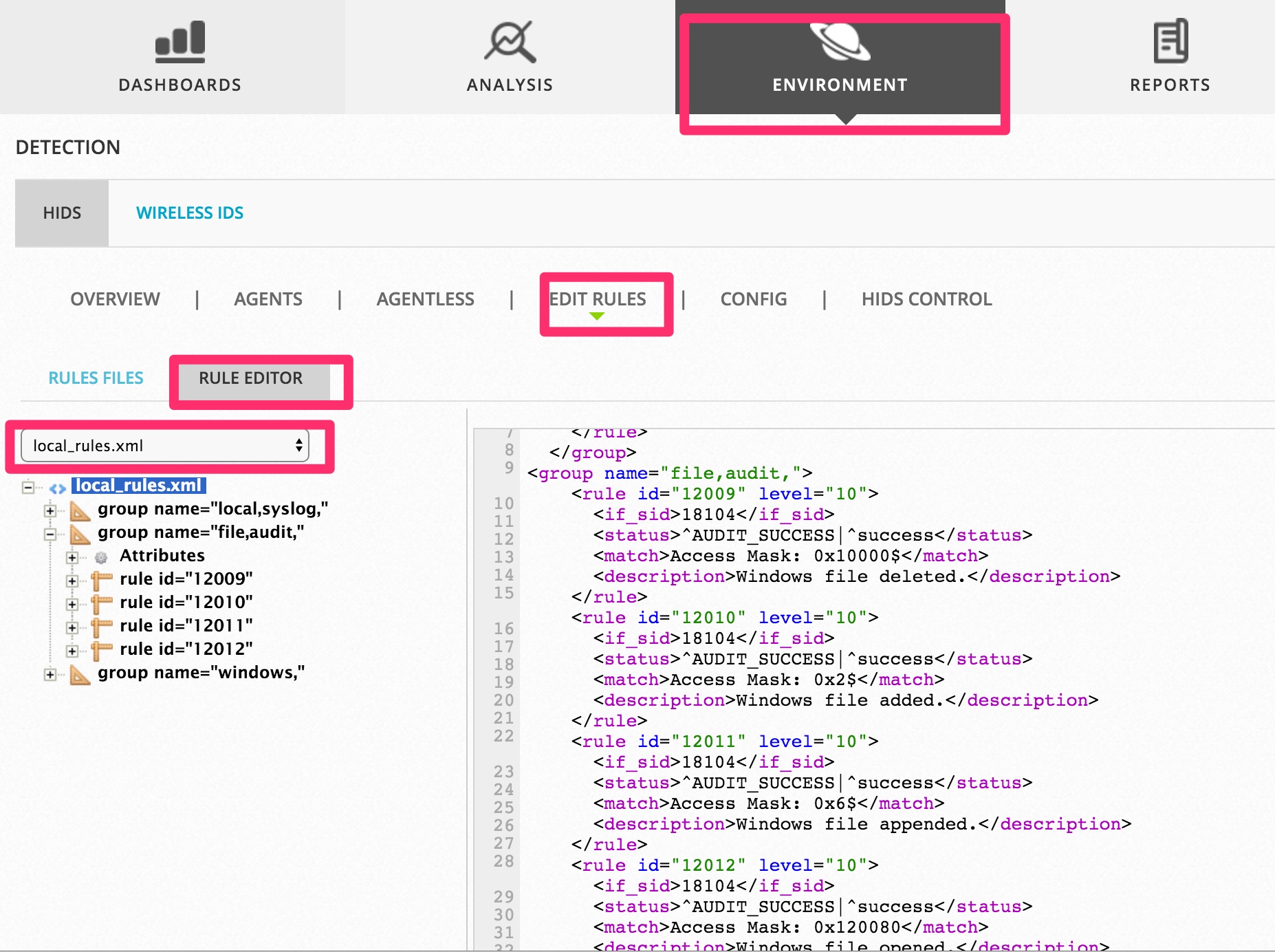
Once done, restart HIDS:
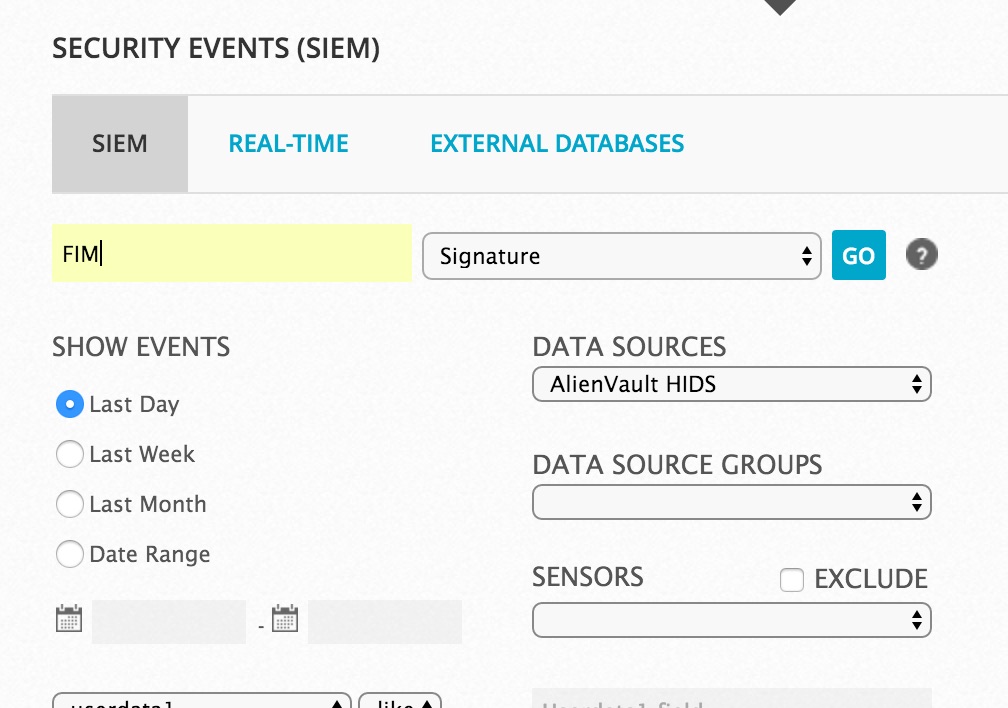
As long as the HIDS restart is good, we can now see events in the SIEM view. (if there’s an error starting HIDS, go back and ensure you pasted and saved properly, and try again.) So go back to Step 3, and generate some file activity. Log back into the SIEM, and go to “Analysis”--> “Security Events”. Select “AlienVault HIDS for the data source, and type FIM into signature, and hit “GO”
Click “Change view” to see the details:
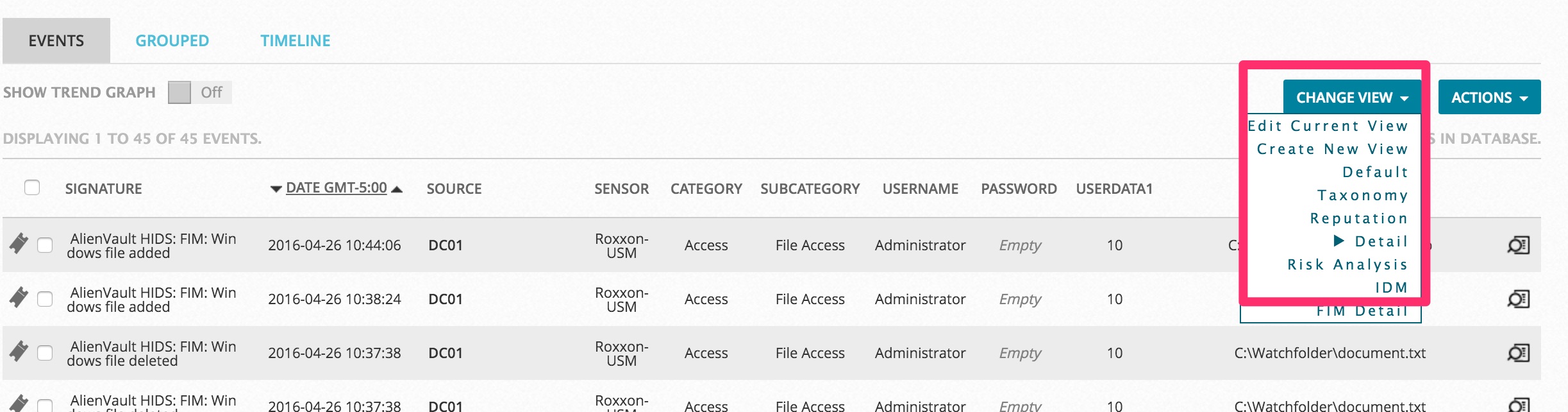
Shazzam! You should now see file audit events!

