Looking at the evolution of ransomware, accepting bitcoin as a payment method is probably taking too long for most common ransomware families.
Not long ago, we have seen a ransomware family that accepts MoneyPak, Ukash, cashU and Bitcoin as payment methods. Its name is CryptoLocker and is detected by Microsoft as Crilock.A.
Just one month after Microsoft released the signature, we have seen a high number of infections and activity of this family.
The sample we analyzed had the CnC hosted on 212[.]71[.]250[.]4 (this is actually a sinkhole, not a CnC). It has a domain generation algorithm, so the CnC could be in a completely different host in just one day.
When the user gets infected, the malware warns and shows some fancy technical information. You can even see a list of files that have been encrypted.
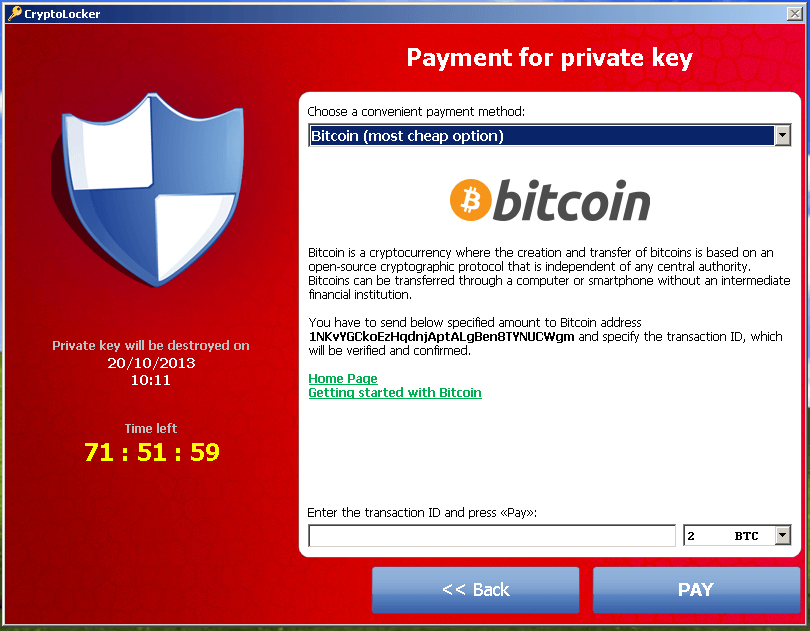
In the next step, you can choose your payment method. The bitcoin option looks like this:
It seems that the owner of this sample is not having great profits at the moment. We can see in Blockchain his transactions.
On the other side, we have seen other Bitcoin addresses used by other samples that had good revenues.
Bitcoin gives criminals the benefict of a valuable and (more or less) anonymous coin. The problem for criminals is that Bitcoins are still mostly used by people with a minimum technical background, who are usually tech savvy, and less affected by malware infections.
In one way or another, you should never pay to release your files. Try to clean your computer with an anvitirus, they even have tools for these kind of infections. Use your backups. Look for help and IT assistance, or even contact your local authorities.