Vulnerability management solutions
Unified Security Management (USM) delivers powerful vulnerability management solutions for your network and public cloud infrastructure, with all-in-one essential security capabilities and continuous threat intelligence updates from the Alien Labs security research team.
Discover Vulnerabilities on Your Critical Assets
Vulnerability management software works to identify the vulnerabilities or “holes” in your critical network and cloud assets, so you can fix them before attackers can exploit them to cause damage or to steal your organization’s data.
New vulnerabilities emerge as your IT landscape evolves, often introduced by system flaws, configuration errors, unauthorized software installs, insecure endpoint devices, delayed software or OS updates, and much more. Thousands of vulnerabilities are discovered every year, requiring never-ending security updates, patches, and other fixes throughout your cloud and on-premises environments.
Like most essential network security work, monitoring your organization’s vulnerability management software can quickly become a full-time job. Yet, most IT teams don’t have dedicated resources who can constantly scan and monitor their environments for vulnerabilities, correlate those vulnerabilities with threat intelligence and real-world attacks, and prioritize and manage remediation as part of a larger IT security program.
But, that’s okay.
Unified Security Management™ (USM™) is designed to help IT and security teams to run an efficient threat and vulnerability management program with an all-in-one unified security platform that centrally monitors AWS and Azure clouds as well as physical and virtual network infrastructure.
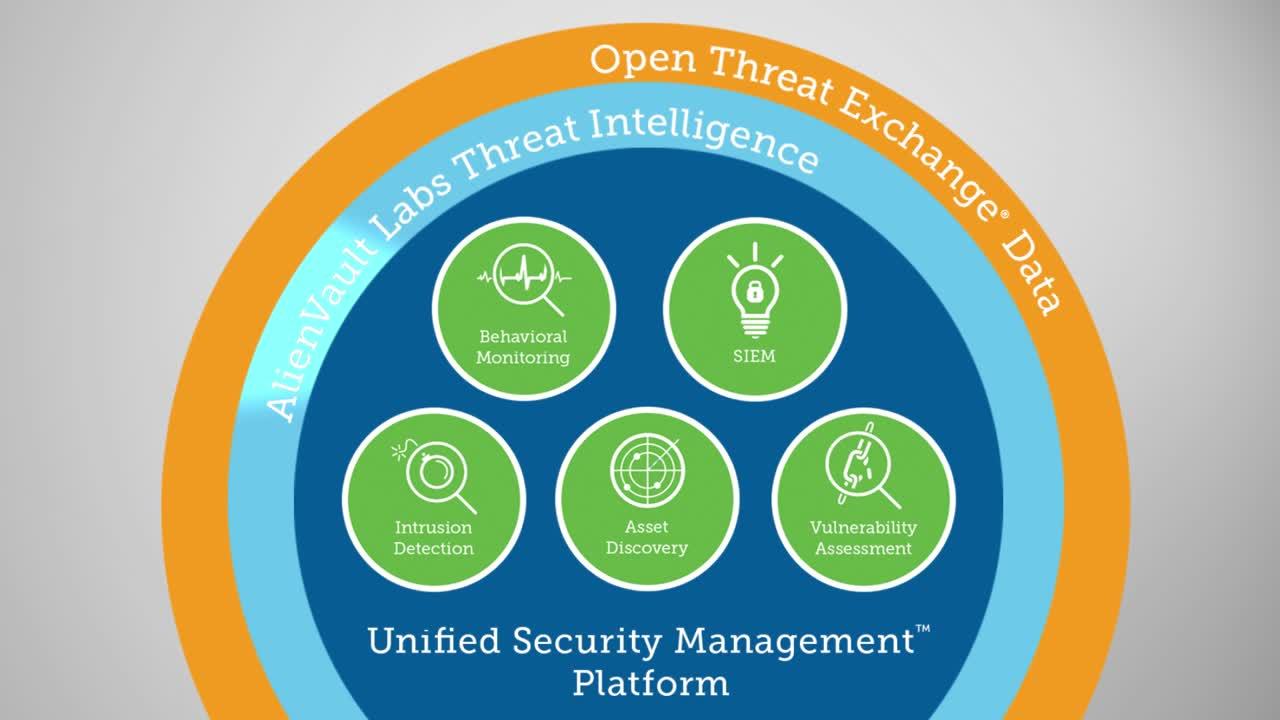
USM combines five essential security capabilities, including asset discovery and inventory, vulnerability assessment, intrusion detection, behavioral monitoring, and SIEM and log management, all on a single, easy-to-use platform. With it, you can easily manage the entire vulnerability lifecycle across your cloud and on-premises environments, rather than adding vulnerability management software to an unwieldy stack of single-point solutions.
With integrated threat intelligence delivered from Alien Labs and the Open Threat Exchange® (OTX™), you can view your vulnerability landscape through the lens of real-world attacks and exploits against vulnerabilities on your critical assets. This allows you to make threat-based decisions about how to respond.
Boost Your Vulnerability Management Program with All-in-One Security Essentials
- Identify assets in your cloud and on-premises environments with built-in asset discovery and inventory tools
- Schedule scans and monitor your assets for new vulnerabilities and weaknesses
- Know which vulnerabilities are actually being exploited with built-in intrusion detection
Align Your Response with Real-world Threat Intelligence from Alien Labs and OTX
- Know which of your vulnerabilities are being exploited in real-world attacks and how
- Get the assurance of vulnerability signature updates delivered continually as new vulnerabilities are identified
Manage Every Step of the Vulnerability Lifecycle from a Single Pane of Glass
- Establish a baseline of your security posture with regularly scheduled, automated scans
- Prioritize your response plan to deal with the most critical assets and the biggest threats first
- Validate resolution with a continuous cycle of scanning and remediation verification
Boost Your Vulnerability Management Capabilities with All-in-One Security Essentials
USM goes beyond traditional security tools to give you the most complete and accurate view of your vulnerability landscape. It combines five essential security capabilities on a unified platform, so you have all the information you need in one location to manage vulnerabilities and prioritize your response.
Discover What’s Connected to Your Environments
Vulnerability management best practices begin with asset discovery and inventory, one of the five essential security capabilities in USM. Before you can identify the vulnerabilities in your environments, you must look at what’s connected to your infrastructure at any given moment. USM uses multiple advanced technologies to identify your connected assets, as well as the operating systems and services installed on them. Because assets may periodically connect and disconnect from an environment, USM continuously scans for assets, giving you a complete and accurate view of your asset inventory at all times.
Asset discovery and inventory creates a foundation for a solid vulnerability management process and ensures that you can run vulnerability scans on all the discoverable assets in your environments, including network devices, virtualized assets, and even rogue assets that you are not aware of.
Continuously Scan and Monitor Your Assets for Vulnerabilities
USM continuously scans and monitors your assets to look for misconfigured or unpatched systems and software, policy violations, malware, and other security issues that can leave your network vulnerable to attacks. With USM, you can easily customize your vulnerability scans in a point-and-click way, selecting the scan frequency, network segments or locations, asset groups, scanning methods, depth of probe, and more. You can schedule scans to run automatically as well as on demand, for example, to validate a recent fix or patch.
Know Which Vulnerabilities are Being Exploited with Intrusion Detection Tools
USM leverages a built-in network intrusion detection system (NIDS) and a host intrusion detection system (HIDS) that identify malicious traffic and patterns of behavior in your network environments. In addition, USM Anywhere™ delivers purpose-built cloud intrusion detection, enabling you to detect threats and vulnerabilities in your AWS and Azure cloud environments.
On their own, NIDS, HIDS, and cloud IDS tools work effectively to get your attention when something suspicious or anomalous occurs. But, when used as part of a unified security solution like USM, these tools give you critical information about the vulnerabilities in your environments that are actually under attack. With it, you can take swift action to mitigate the threat and prevent further exploitation of highly targeted vulnerabilities on your critical systems and services.
Manage Every Step of the Vulnerability Lifecycle from a Single Pane of Glass
Attackers look for the easiest way possible to enter your environments. Most often, that entrance is through a known vulnerability that was never properly patched or fixed, effectively leaving the door wide open to intruders.
When a threat occurs, IT and security professionals must look at every step in the vulnerability lifecycle to understand where and why the process failed. There are many reasons why smart organizations fail to fix a vulnerability before it’s exploited –
- The vulnerability emerged between quarterly scans and wasn’t discovered until after it was exploited.
- They did not consider the significance of the vulnerable asset and did not prioritize its remediation accordingly.
- The lag time between the discovery of the vulnerability and the remediation action was too great, allowing an attacker to infiltrate.
- They did not have a way to verify that the patch was completed by a different team responsible for it.
- They did not have a way to validate that the patch correctly resolved the vulnerability.
With USM, you can address these challenges and manage every step of the vulnerability lifecycle from a single pane of glass.
USM takes an asset-oriented approach to vulnerability lifecycle management. The all-in-one platform constantly scans your critical infrastructure to identify new assets, so you always have the most complete and accurate asset inventory available for your vulnerability scans. You can run vulnerability scans on specific asset groups, such as assets in scope of compliance requirements or all assets in your home office.
Because USM combines all asset and vulnerability information with threat intelligence from the Alien Labs Security Research Team, you can prioritize your vulnerability response activities according to the significance of the vulnerable assets and any real-world exploits, rather than relying solely on a static high-to-low vulnerability scoring system.
For many reasons, it’s not always a best practice to respond immediately to your known vulnerabilities. For example, systems with high availability or low latency requirements cannot readily be taken offline to install a patch. Instead, mitigation becomes the best practice. With USM’s asset-oriented security, you gain the assurance of having complete visibility of the vulnerable asset, so you can monitor it closely from all angles to mitigate exploits until a resolution is available.
Finally, USM’s continuous vulnerability scanning capabilities enable you to verify and validate your vulnerability remediation activities in a simple and productive way.