AWS security monitoring and compliance management
USM Anywhere delivers security and compliance management for the cloud in the cloud.
Benefits
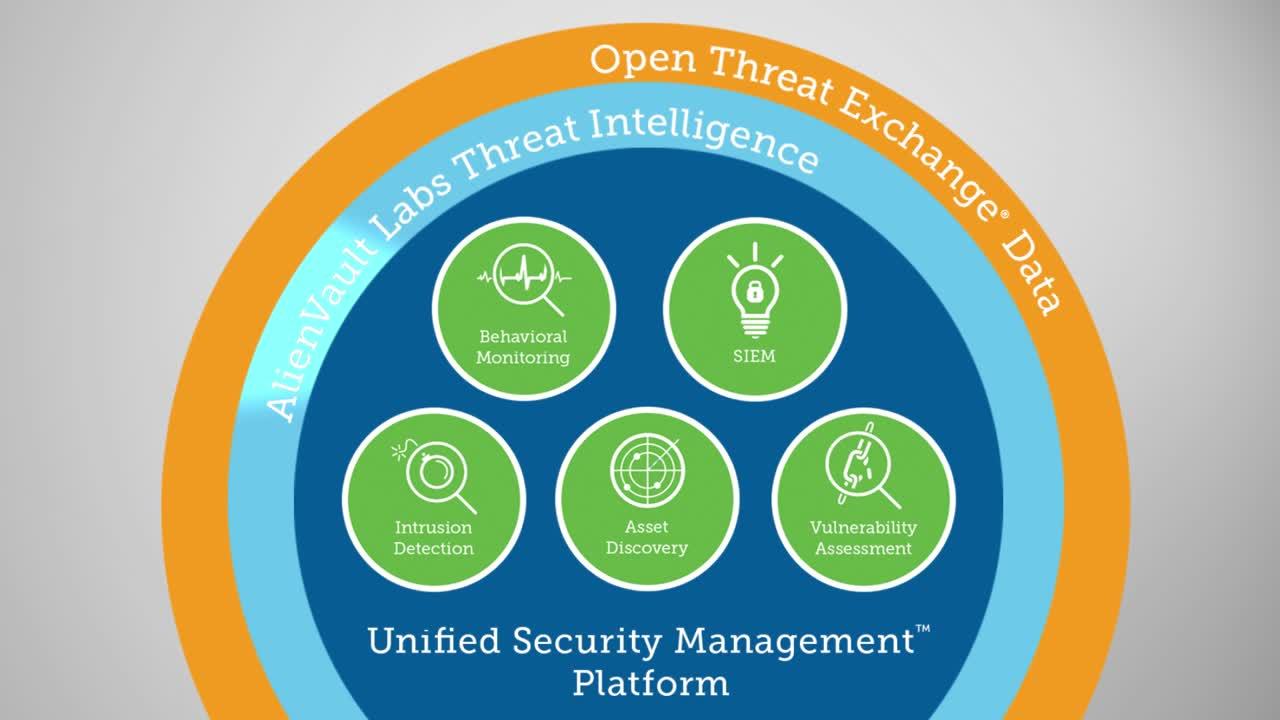
Essential security capabilities for the AWS cloud
Most enterprises - whether large or small - are quickly reaping the benefits of the cloud. Cloud service providers, like Amazon Web Services (AWS), offer flexibility and scalability to businesses in every industry. Unfortunately, IT security pros lose visibility and control over the data flowing in and out of the cloud, as well as when and how new workloads and instances are spun up. Yet, they’re still responsible for AWS security and compliance best practices.
The reality is traditional, network-centric security capabilities (e.g. intrusion detection) fall apart when migrated to the cloud, and some like vulnerability assessment - are prohibited by Amazon unless an AWS Vulnerability / Penetration Testing Request Form is filled out and approved.
USM Anywhere™ overcomes these security and compliance challenges and more. In fact, we’ve optimized our AWS sensor to address the biggest cloud security issues in the simplest way.
Monitor, detect, and investigate AWS security issues
Detect and alert on abnormal behavior within AWS, run continuous vulnerability assessments and immediately discover new assets or misconfigurations.
Accelerate and demonstrate AWS security compliance
Deploy in minutes to gain immediate visibility and run detailed reports on AWS security and compliance for PCI DSS, ISO 27001, NERC CIP, and more.
Integrate your AWS and on-premises security policy
Eliminate blind spots with unified security monitoring and respond to incidents quickly with integrated threat intelligence from AT&T Alien Labs.
Monitor, detect, and investigate AWS security issues
According to Gartner Research, "Through 2020, 80% of cloud breaches will be due to customer misconfiguration, mismanaged credentials or insider theft, not cloud provider vulnerabilities." It's not the nature of the cloud that introduces security risks, but rather the lack of control that it brings. Anyone in your organization (with a credit card) can deploy new applications, exposing your company and its data to risk - and you may never even know about it. And yet, you’re still responsible for protecting this data.
To do that, you need to know things like:
- Which users are accessing AWS workloads?
- Where are they signing in from?
- Are hackers scanning my infrastructure?
- Has anyone compromised my credentials?
- Did anyone mess with my security groups?
- Are my servers communicating with known command and control servers?
- Do any of my machines have known vulnerabilities?
USM Anywhere gives you the essential visibility and control you need for AWS security and compliance. Unlike traditional security approaches that try to retrofit their network-centric approach to an AWS universe, USM Anywhere is optimized for AWS with support for:
- CloudTrail monitoring & alerting
- S3 access log monitoring & alerting
- ELB access log monitoring & alerting
- AWS API asset discovery
- AWS-native cloud intrusion detection
- AWS vulnerability assessment
- AWS infrastructure assessment
1 Gartner Research Paper, Best Practices for Securing Workloads in Amazon Web Services, April 2015
Get multiple security capabilities in one unified platform




Accelerate and demonstrate AWS security compliance
Compliance mandates like PCI DSS and NERC CIP require that you have implemented the essential security controls to protect sensitive data in your environment. Auditors will want to see proof that you know:
- Which assets contain sensitive data
- Who can access this data (and that they are authorized)
- How assets are configured and whether there are any known vulnerabilities present
- What threats exist and how to respond to them
Answering these questions for AWS assets requires that you have the capability to discover new assets, validate Security Group configurations, monitor VPC flow logs, run vulnerability scans and reports, and respond to emerging threats. And bring all that data together in a meaningful way so that you can pass that next audit, as well as maintain a secure posture in this dynamic environment.
USM Anywhere delivers the tools you need in one place so you can achieve a confident security posture and compliance, saving you time and money while benefiting from the speed and agility of AWS. You can deploy USM Anywhere within minutes, and have detailed compliance reports to provide to your auditor as needed.
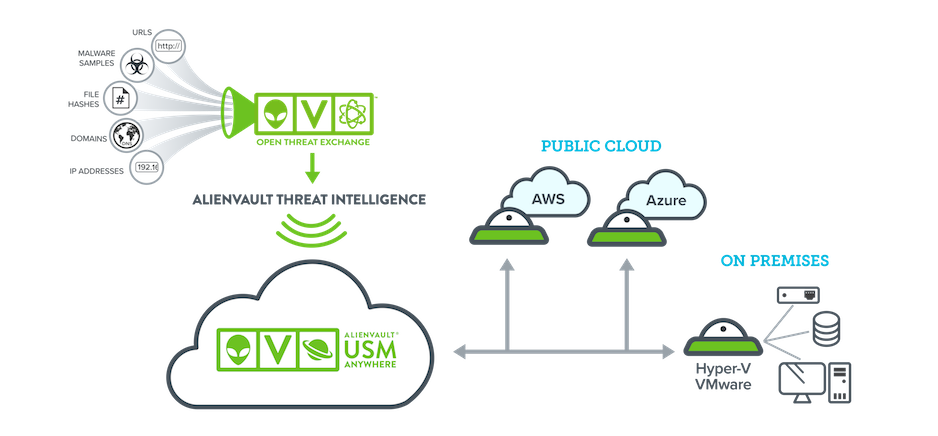
Integrate your AWS and on-premises security policy
Nearly all companies have hybrid environments, where some data and apps have migrated to AWS, and others remain on-premises. In this context, it’s essential to have a complete picture into the security posture of this data, as well as the servers and apps that it flows through. But if you’re managing two separate security monitoring infrastructures - one for on-premises systems and another for AWS - you’re working twice as hard and still missing the big picture.
USM Anywhere overcomes this challenge by unifying security monitoring across environments - whether you’re using AWS, Azure, or have on-premises infrastructure to monitor as well. Plus, as a cloud-based security management solution, you can scale your threat detection and response capabilities as your hybrid environment changes, and pay for only what you need, when you need it. With this level of scalability, you can accelerate AWS incident response as well as reduce cost and complexity.
Simple, scalable AWS security and compliance
Centralize AWS security monitoring
USM Anywhere automatically collects and alerts on security data from critical AWS services such as CloudTrail, CloudWatch, and S3 and ELB access logs, centralizing and simplifying your AWS security monitoring.
Get threat intelligence built for AWS
Alien Labs’ threat intelligence includes AWS-specific correlation rules, so you can detect the latest threats, vulnerabilities, misconfigurations, and anomalous behaviors in your AWS environment.
Scale security with your cloud
USM Anywhere is a cloud-hosted SaaS platform that readily scales as your IT environment evolves. It’s fast and easy to deploy with no hardware to install.
Eliminate blind spots and shadow IT
Centrally monitor your multi-cloud and on-prem assets with a unified platform to ensure continuous threat coverage and the elimination of shadow IT as you migrate data and services to the cloud.
Discover DevOps-friendly security
Support your agile development with automated security monitoring across build, test, and production environments and leverage our integrations with DevOps tools like PagerDuty, Slack, Jira and others.
Simplify compliance in the cloud
Ensure your AWS environment adheres to key regulatory or industry compliance mandates, such as PCI DSS, HIPAA, or GDPR. Learn how USM Anywhere simplifies IT security compliance in AWS.
Secure your AWS environment
USM Anywhere provides complete cloud security management for your AWS environments. It includes all of the essential capabilities for monitoring cloud security and quickly identifying malicious or suspicious activity in your AWS cloud infrastructure.