AWS PCI DSS compliance
Accelerate AWS PCI DSS compliance with AlienVault USM Anywhere.
Simple, scalable AWS security and compliance
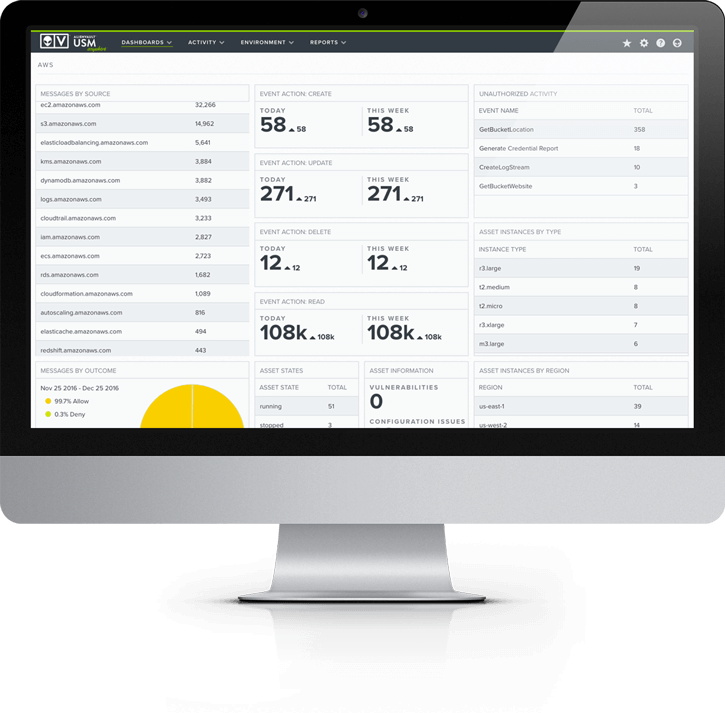
Centralize AWS security monitoring
USM Anywhere automatically collects and alerts on security data from critical AWS services such as CloudTrail, CloudWatch, and S3 and ELB access logs, centralizing and simplifying your AWS security monitoring.
Get threat intelligence built for AWS
Alien Labs’ threat intelligence includes AWS-specific correlation rules, so you can detect the latest threats, vulnerabilities, misconfigurations, and anomalous behaviors in your AWS environment.
Scale security with your cloud
USM Anywhere is a cloud-hosted SaaS platform that readily scales as your IT environment evolves. It’s fast and easy to deploy with no hardware to install.
Eliminate blind spots and shadow IT
Centrally monitor your multi-cloud and on-prem assets with a unified platform to ensure continuous threat coverage and the elimination of shadow IT as you migrate data and services to the cloud.
Discover DevOps-friendly security
Support your agile development with automated security monitoring across build, test, and production environments and leverage our integrations with DevOps tools like PagerDuty, Slack, Jira and others.
Discover a Faster Path to AWS PCI DSS Compliance & Security
Achieving AWS PCI DSS Compliance is a must-have for any organization that handles consumers’ credit card data in their AWS cloud environment. To get there, you must prove that you have in place robust security controls to monitor your logs, detect vulnerabilities, protect cardholder data, and much more. This can be a big challenge for resource-limited IT security teams, especially if you need to get ready for a fast-approaching PCI DSS compliance audit.
AlienVault® Unified Security Management™ (USM) helps you to simplify and accelerate your AWS PCI DSS Compliance by combining multiple essential security capabilities onto a single platform that supports many PCI DSS requirements, including asset discovery, vulnerability assessment, intrusion detection, behavioral monitoring, SIEM, and log management. The built-in PCI DSS compliance reports in AlienVault USM make it simple to demonstrate compliance in an audit and to continuously monitor your compliance program afterwards.
AlienVault USM centralizes PCI DSS compliance and security management across your cloud, on-premises, and hybrid environments. Its native AWS security monitoring capabilities allow you to dynamically discover your AWS assets, including those in scope of your AWS PCI DSS compliance environment. It also collects, analyzes, and securely stores log data from CloudTrail, CloudWatch, VPC Flow Logs, ELB logs, S3 Access Logs, and system logs in the AlienVault Secure Cloud.
AlienVault USM has been certified compliant to PCI DSS, so you can pursue your own AWS PCI DSS compliance certification with the assurance that AlienVault has the proper security controls in place to securely transmit, process, and store your data in accordance with PCI DSS requirements.
Streamline AWS PCI DSS Compliance with One Unified Solution
The AlienVault USM platform cuts through the expense and complexity of having multiple security tools to demonstrate AWS PCI DSS Compliance. It delivers multiple essential security capabilities in one unified, affordable solution, so you prepare for your compliance audit faster and more easily.
AlienVault USM satisfies many PCI DSS requirements through unified asset discovery and inventory, vulnerability assessment, intrusion detection, behavioral monitoring, SIEM event correlation, and log management—all in a single pane of glass. Discover which PCI DSS goals you can realize with AlienVault USM.
Build and Maintain a Secure Network and Systems
The AlienVault USM platform monitors your AWS cloud environment as well as your on-premises environment, allowing you to monitor configuration changes to your network firewalls and routers, identify weak or default passwords, and detect AWS configuration issues that may leave you exposed.
Maintain a Vulnerability Management Program
The built-in asset inventory, vulnerability assessment, threat detection, and log analysis capabilities in the AlienVault USM platform provide the continuous security visibility you need to detect and respond to intrusions and vulnerabilities efficiently.
Implement Strong Access Control Measures
Powerful SIEM event correlation and log analysis in the USM platform captures all user account activities on critical systems in AWS, in your data center, and on cloud applications like Office 365 and G Suite. This includes the collection and correlation of valid and invalid authentication attempts, so you always know who is trying to access your cardholder data environment (CDE).
Regularly Monitor and Test Networks
You should regularly monitor user access to your AWS data processing resources and test for vulnerabilities in your environment, not only to satisfy requirements for AWS PCI DSS compliance but also for critical security monitoring activities. AlienVault USM combines vulnerability assessment, event correlation, and log management to give you the security visibility your need in a single pane of glass.
Maintain an Information Security Policy
The AlienVault USM platform helps you to detect breaches sooner and to respond faster by enabling automated incident response and giving you all the relevant security data you need at your fingertips along with response guidance and continuous threat intelligence updates. This supports your efforts to maintain a strong information security policy program.
Prove Compliance for Even the Most Challenging Requirements
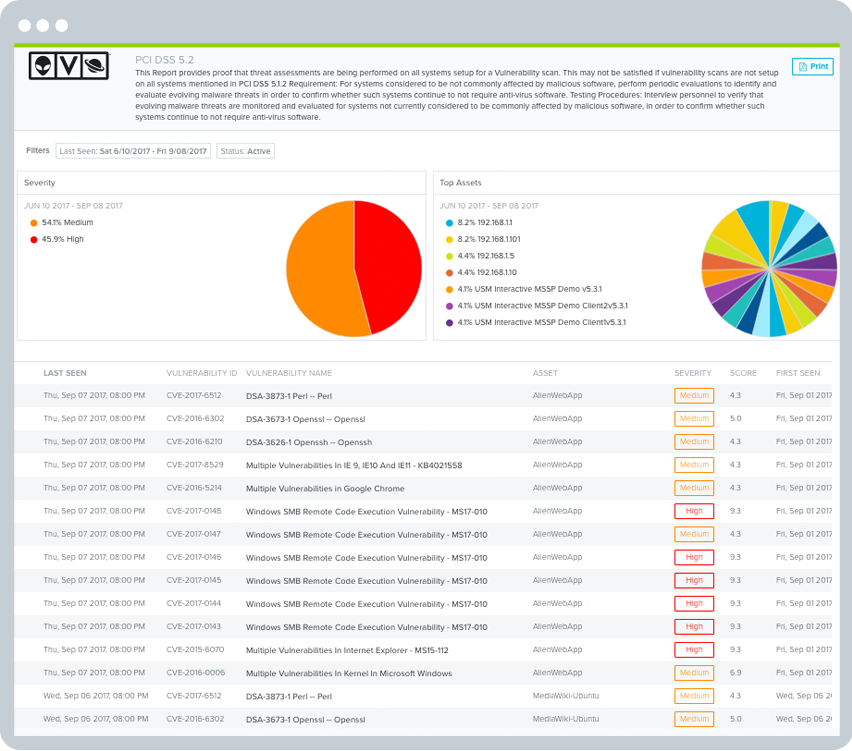
Malware Protection: PCI DSS Requirement 5
AlienVault USM helps you identify systems susceptible to known vulnerabilities, or that may not have antivirus software installed or operational. Its intrusion detection capabilities monitor for indicators of a malware-based threat. When malware is detected, AlienVault USM can automate incident response actions to isolate infected systems and block malicious domains.
Vulnerability Assessment: PCI DSS Requirements 6 and 11
AlienVault USM delivers vulnerability assessment, so that you can find and fix weak spots in your cloud and on-premises environments. Together, AlienVault USM’s asset discovery and vulnerability assessment tools simplify security visibility by unifying the data gathered in asset and vulnerability scans with known vulnerability information. In addition, its file integrity monitoring (FIM) tool alerts users to changes to critical files that may indicate a breach.
Incident Response Planning: PCI DSS Requirement 12
Make sure the right people get notified to respond quickly in the case of an incident. USM Anywhere provides the alerting you need to identify threats, respond to the threats, and keep track of decisions made about the threats. With USM Anywhere and its AWS-native sensor, you get 24X7 coverage.
Logging and Reporting: PCI DSS Requirement 10
Sections 10.1 - 10.4 deals with collecting audit logs, tracking access to cardholder data, actions taken by admins, failed logins, and manipulation of the audit trail. USM Anywhere timestamps the data as required in Section 10.4.
Section 10.5 requires that audit trails be secured so they cannot be altered. In AlienVault USM, log data is securely stored with a “Write Once, Read Many (WORM)” method, ensuring the integrity of your raw logs for forensics and compliance needs.
Requirement 10.6 requires you review your log data and security events for anomalies or suspicious activity. AlienVault USM collects data from your applications, servers, and devices from across your on-premises and cloud environments and cloud applications. Customizable views, built-in and customizable PCI DSS reports, and advanced correlation capabilities simplify the ability to review data, so you can easily monitor and report on threats and anomalies.
Section 10.7 mandates that you retain audit history for at least one year, with a minimum of three months immediately available for analysis. USM Anywhere stores data online for up to 90 days and retains the data long term for a full year. This provides the advanced log management and secure long-term raw log retention for AWS PCI DSS compliance, even in high-volume environments.
Discover How AlienVault USM Supports PCI DSS Requirements
PCI Requirement
PCI Sections AlienVault USM Addresses
How AlienVault USM Helps
1. Install and maintain a firewall configuration to protect cardholder data.
1.1, 1.2, 1.3
- Built-in asset discovery provides a dynamically updated inventory of assets across your cardholder data environment, ensuring only authorized endpoints are deployed.
- Capture events relating to configuration changes on firewalls and routers, including when user accounts get updated.
- Discover unauthorized communications, such as between untrusted networks and systems within the cardholder data environment.
2. Do not use vendor-supplied defaults for system password and other security parameters.
2.1, 2.2, 2.3, 2.4, 2.6
- Identify use of default system accounts on Windows machines.
- Non-customizable File Integrity Monitoring can detect changes to predetermined paths in Windows and Linux systems.
- Identify vulnerabilities such as where an application may have a cryptographic algorithm vulnerability and recommend if patches or workarounds are available.
- Help identify specific services, ports, systems, and users
- Built-in asset discovery provides a dynamically updated inventory of what systems are operational in your environment, and what software is running on each.
- Discover and monitor assets running on-premises and in cloud environments (including Azure, VMware, Hyper-V, AWS, GCP)
3. Protect stored cardholder data
3.6, 3.7
- Monitor for changes to Office 365 policies, including data loss prevention (DLP), information management, and more.
- File Integrity Monitoring can detect when SSH or similar cryptographic keys are modified.
- Unified log review and analysis, with triggered alarms for high-risk systems.
4. Encrypt transmission of cardholder data across open, public networks
4.1, 4.3
- Identify when network traffic goes to unauthorized networks.
- Identify systems using compromised or insecure protocols that may increase their risk of being attacked.
- Monitor for changes to Office 365 policies, including Information Management and more.
5. Protect all systems against malware and regularly update antivirus software or programs
5.1, 5.2, 5.3, 5.4
- Identify systems susceptible to known vulnerabilities, or that may not have antivirus installed and/or operational.
- Identify for indicators of malware-based compromise, and orchestrate manual and automated actions to isolate infected systems and block malicious domains.
- Monitor and store events from antivirus solutions that could indicate a compromise, or attempt to disable antivirus software.
- Monitor for changes to Office 365 policies, including Information Management and more.
6. Develop and maintain secure systems and applications
6.1, 6.2
- Identify systems susceptible to known vulnerabilities, with systems ranked as 'high,' 'medium,' and 'low' risk vulnerabilities.
- Identify patches or workarounds available to vulnerable systems.
7. Restrict access to cardholder data by business need to know
7.1, 7.3
- Identify attempts to access systems using privileged accounts.
- Identify escalation of privilege attempts.
- Monitor for changes to Office 365 policies, including Information Management and more.
8. Identify and authenticate access to system components
8.1, 8.2, 8.5
- Aggregate logs and events from systems, applications, and devices from across your on-premises and cloud environments.
- Identify attempts to use retired or default user credentials.
- Monitor and alarm on Group Policy errors.
9. Restrict physical access to cardholder data
N/A
- Not applicable.
10. Track and monitor all access to network resources and cardholder data
10.1, 10.2, 10.3, 10.4, 10.5, 10.6, 10.7, 10.8
- Aggregate, analyze, and archive logs and events from systems, applications, and devices from across your on-premises and cloud environments.
- Identify logon success and failures.
- Identify privilege escalation attempts.
- Identify where systems are out of sync with the current time and/or Domain Controller, or for non-typical traffic on port 123.
- Identify unauthorized attempts to access or modify key logs.
- Identify where security tools, such as antivirus and firewalls, have been disabled or have failed to start.
- Captures all user account creation and modification activities.
11. Regularly test security systems and processes
11.1, 11.2, 11.4, 11.5, 11.6
- Assess systems for vulnerabilities, and where found rank them as 'high', 'medium,' and 'low' risk.
- Monitor access to and attempt to modify system and application binaries, configuration files, and log files.
- Monitor user and administrator activities in cloud environments such as Azure and AWS, and within cloud applications such as Office 365.
- Apply labels to alarms.
- Generate incident tickets within popular solutions like ServiceNow, directly from within the USM Anywhere console.
12. Maintain a policy that addresses information security for all personnel
12.1, 12.5, 12.8
- Monitor for changes to Office 365 policies, including Data Leakage Protection (DLP), information management, and more.
- Monitor all administrative activities through popular authentication and authorization solutions like Azure Active Directory.
- Monitor network traffic for violations of policy, such as communications that cross your cardholder data environment perimeters.
Secure your AWS environment
USM Anywhere provides complete cloud security management for your AWS environments. It includes all of the essential capabilities for monitoring cloud security and quickly identifying malicious or suspicious activity in your AWS cloud infrastructure.






