AWS vulnerability scanning
Simplify AWS vulnerability scanning with USM Anywhere.
Benefits
An automated, purpose-built vulnerability scanner for your AWS cloud environment
Securing data in AWS environments remains a challenging task, especially since Amazon operates on a ‘shared responsibility’ security model. This means that while Amazon physically secures its cloud infrastructure, the customer is responsible for securing their applications and data. Achieving security in the AWS cloud requires diligent monitoring of your AWS environment to identify changes that can leave your assets vulnerable to exploit. Failure to put in place essential security controls can leave you susceptible to an attack. Additionally, it can be time-consuming and frustrating to follow the procedural requirements that Amazon has put in place to conduct traditional vulnerability scanning of your AWS environment.
USM Anywhere™ addresses this pain point with a purpose-built sensor that is designed to work with the AWS ‘shared responsibility’ model, automatically performing vulnerability scans in your AWS environment. This AWS-native sensor allows you to ensure quick and continuous vulnerability assessment.
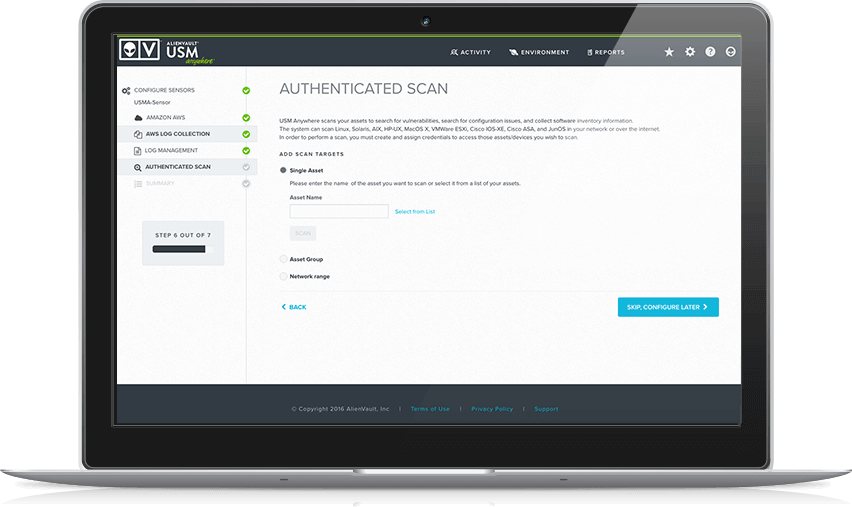
Easy configuration and automatic scanning
Identify AWS vulnerabilities and automatically scan your AWS environment including assets, security groups, and configurations.
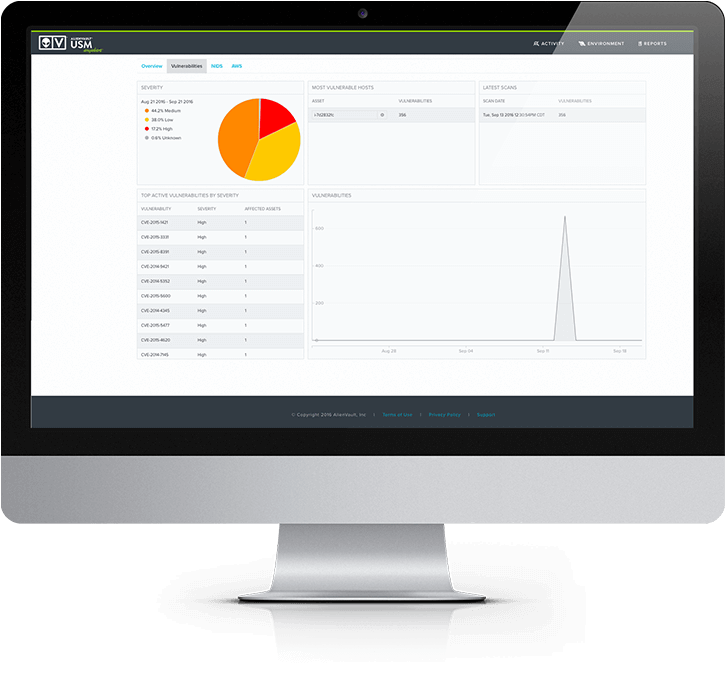
Intuitive dashboard
Gain visibility across cloud and on-premises environments, full vulnerability and threat context and step-by-step remediation guidance.
Integrated threat intelligence updates
Spot the latest exploits targeting your AWS environment and focus on responding to validated threats rather than researching every alert.
Easy configuration and automatic scanning
Scanning your AWS environment for vulnerabilities and configuration issues can seem like a daunting task given that you can’t use traditional scanning tools in an AWS environment without paperwork or approvals. While Amazon sets up methods to allow traditional vulnerability scanning in your AWS environment, it is difficult and time consuming to satisfy the procedural requirements every time you want to run a scan. Most IT teams do not even attempt to conduct AWS vulnerability scans, meaning that essential vulnerability testing of their AWS environment often does not occur.
You need a security monitoring solution that automates AWS vulnerability scanning and threat detection. USM Anywhere provides a unified security platform for your AWS environment that simplifies threat detection by automatically performing vulnerability scanning on assets within your AWS environment. USM Anywhere’s AWS-native sensor resides in your AWS environment and delivers the continuous AWS vulnerability assessment you need to ensure that vulnerabilities and misconfigurations don’t slip through the cracks and leave you exposed.
Intuitive dashboard
Once you’ve completed the AWS vulnerability scan, you need to develop a prioritized response plan that identifies the vulnerabilities, configuration issues and access control issues and their potential impact to your environment. Doing this efficiently requires expert knowledge of not only the exploit methods but the affected assets and systems as well.
The USM Anywhere platform with a USM Anywhere Sensor deployed in your AWS infrastructure gives you the ability to find the vulnerabilities that matter most. From the USM Anywhere console, you can quickly identify the critical assets that have vulnerabilities. The vulnerability name, asset, Common Vulnerability Enumeration (CVE), and severity are displayed to identify the most severe vulnerabilities first. From the Vulnerabilities dashboard, you can see at-a-glance which assets are most vulnerable so you can deal with the important, most critical assets first.
Additionally, USM Anywhere is integrated with the Alien Labs Open Threat Exchange (OTX), the world’s first truly open threat intelligence community that enables collaborative defense with actionable, community-powered threat data. Information about each vulnerability can be accessed directly from the platform interface. For a more detailed view of information, USM Anywhere allows you to click through directly to OTX to see detailed information about the vulnerability, how it is used to exploit a system, and reference information collected and known. This provides you with all the information you need to make a decision and respond to the discovered vulnerability.
Secure your AWS environment
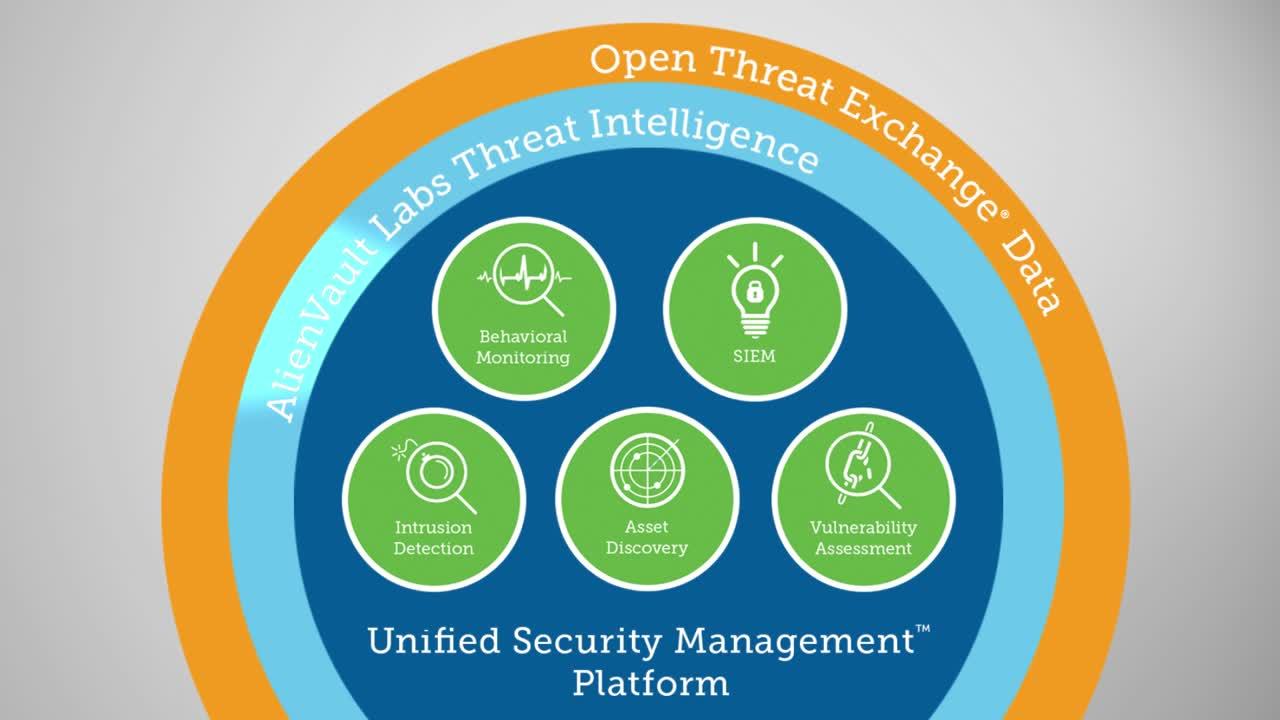
USM Anywhere provides complete cloud security management for your AWS environments. It includes all of the essential capabilities for monitoring cloud security and quickly identifying malicious or suspicious activity in your AWS cloud infrastructure.
Simple, scalable AWS security and compliance
Centralize AWS security monitoring
USM Anywhere automatically collects and alerts on security data from critical AWS services such as CloudTrail, CloudWatch, and S3 and ELB access logs, centralizing and simplifying your AWS security monitoring.
Get threat intelligence built for AWS
Alien Labs’ threat intelligence includes AWS-specific correlation rules, so you can detect the latest threats, vulnerabilities, misconfigurations, and anomalous behaviors in your AWS environment.
Scale security with your cloud
USM Anywhere is a cloud-hosted SaaS platform that readily scales as your IT environment evolves. It’s fast and easy to deploy with no hardware to install.
Eliminate blind spots and shadow IT
Centrally monitor your multi-cloud and on-prem assets with a unified platform to ensure continuous threat coverage and the elimination of shadow IT as you migrate data and services to the cloud.
Discover DevOps-friendly security
Support your agile development with automated security monitoring across build, test, and production environments and leverage our integrations with DevOps tools like PagerDuty, Slack, Jira and others.
Simplify compliance in the cloud
Ensure your AWS environment adheres to key regulatory or industry compliance mandates, such as PCI DSS, HIPAA, or GDPR. Learn how USM Anywhere simplifies IT security compliance in AWS.