AWS intrusion detection system 〈IDS〉
Automate AWS intrusion detection (IDS) to quickly identify malicious activity.
Benefits
Take control of your cloud security monitoring, management and risks
As organizations of every size are adopting cloud services, attackers have followed suit. But a core problem exists in AWS – there is no way to get complete access to the low-level network traffic using traditional IDS detection methods. However, this challenge can be overcome by accessing the AWS control plane. In doing so, Unified Security Management (USM) Anywhere™ can provide core Intrusion Detection (IDS) capabilities in AWS cloud environments.
Security benefits of USM Anywhere for AWS cloud environments include:
- Full visibility into every operation that is going on in all of your AWS accounts
- Identify which users have accessed your AWS environment
- Check and alert on CPU spikes on your AWS instances
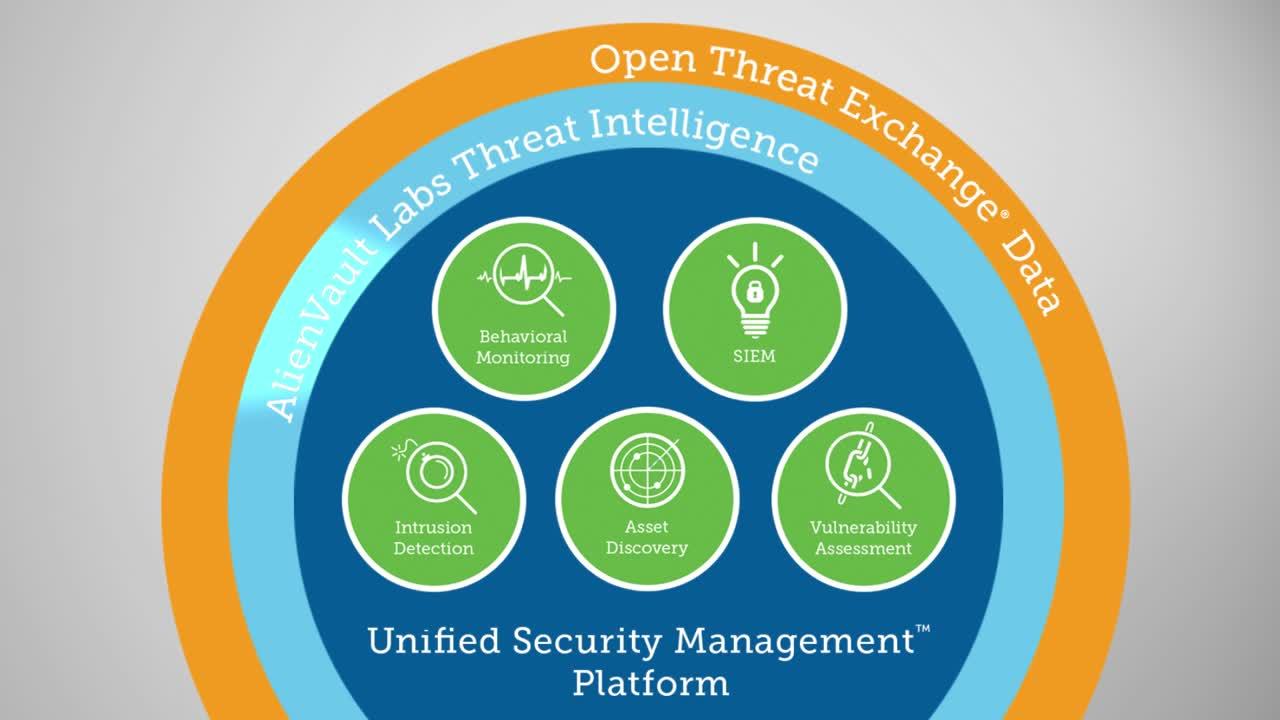
USM Anywhere unifies the essential security capabilities to enable cloud security management in a single platform:
Built for AWS from the ground up
Cloud-native intrusion detection (IDS) designed to monitor AWS environments and to work with Amazon’s shared responsibility model.
Log management for compliance
Achieve compliance with PCI DSS, FISMA, FedRAMP, ISO 27001, NERC CIP, or GLBA requirements and secure collection and retention of raw and normalized logs.
Integrated threat intelligence updates
Focus on responding to real threats rather than researching every alert with continuously updated threat intelligence from Alien Labs.
Built for AWS from the ground up
In traditional environments, the network provides a common chokepoint to monitor your environment, a feature that isn’t typically available in the cloud. However, to our advantage, in AWS, the network infrastructure is largely abstracted away.
Beyond simply providing viable alternatives for the core IDS use cases, AWS also presents a new opportunity for you to improve the monitoring you have done in the past. When you consider an IDS solution for AWS, there is a new chokepoint (similar to the network layer in the past) that you can take advantage of called the control plane.
In software-defined networking (SDN) the data and control plane is decoupled. This allows programmatic access to the control plane that makes network administration much more flexible.
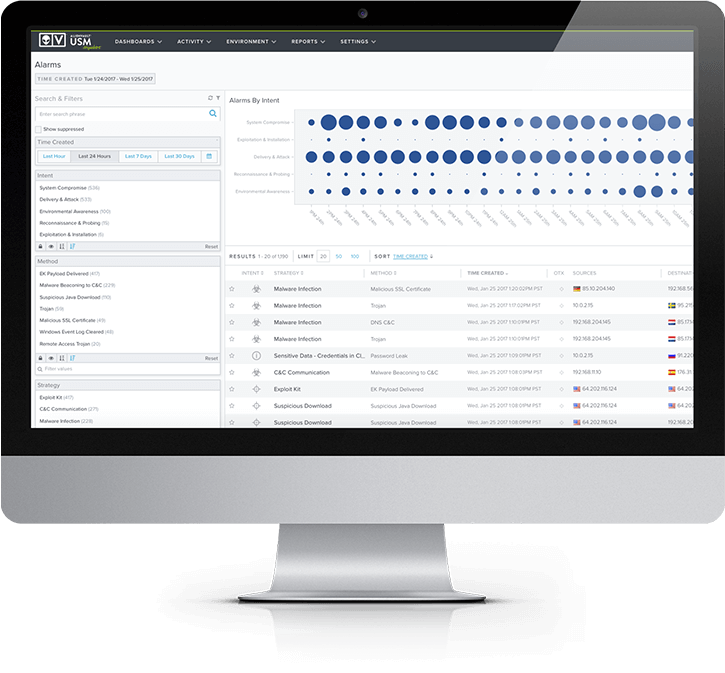
USM Anywhere purpose-built AWS sensors have built-in IDS capabilities that leverage the control plane, giving you full visibility into every operation that is going on in your AWS ‘data center’. This allows you to answer important questions such as:
- Which employee has accessed my AWS environment? Was it really them?
- Are all of my AWS-based systems sending me their operational logs for analysis?
- Can I automatically provision a new system I am spinning up into my security monitoring system?
- Has the CPU spiked on any of my AWS machines in the last hour?
- Who set up this server?
Log management for compliance
Often the drive for AWS intrusion detection is to meet the requirements of regulatory compliance – in particular PCI DSS Requirement 11.4.
Requirement number 11.4 states: “Use intrusion detection and/or intrusion-prevention techniques to detect and/or prevent intrusions into the network. Monitor all traffic at the perimeter of the cardholder data environment as well as at critical points in the cardholder data environment, and alert personnel to suspected compromises.”
The intrusion detection in functionality for AWS within USM Anywhere for AWS cloud environments helps you attain PCI compliance with analysis of log data on systems within the cardholder data environment or otherwise in scope for PCI DSS. This visibility, combined with the analysis of the OS-level logs, makes detection of malware and other threats to key information systems possible.
Integrated threat intelligence updates
USM Anywhere for AWS cloud environments provides IT security analysts with an AWS-native IDS solution that includes the best threat detection and response capabilities. This is powered by expert threat intelligence generated by the Alien Labs team.
Alien Labs research is supplemented with data from our Open Threat Exchange (OTX) which is the largest and most authoritative crowd-sourced threat intelligence exchange globally.
Threat Intelligence updates are published continuously by the Alien Labs team to the USM for AWS platform in the form of:
- Correlation directives
- Vulnerability signatures
- Asset discovery signatures
- Incident response templates
This provides your team with the needed information about threat actors, their methods, infrastructure, and tools making it easier for you to monitor your AWS infrastructure without having to be experts in all threats in the wild. Effectively, Alien Labs becomes an extension to your team, delivering actionable threat intelligence to where you need it most.
Simple, scalable AWS security and compliance
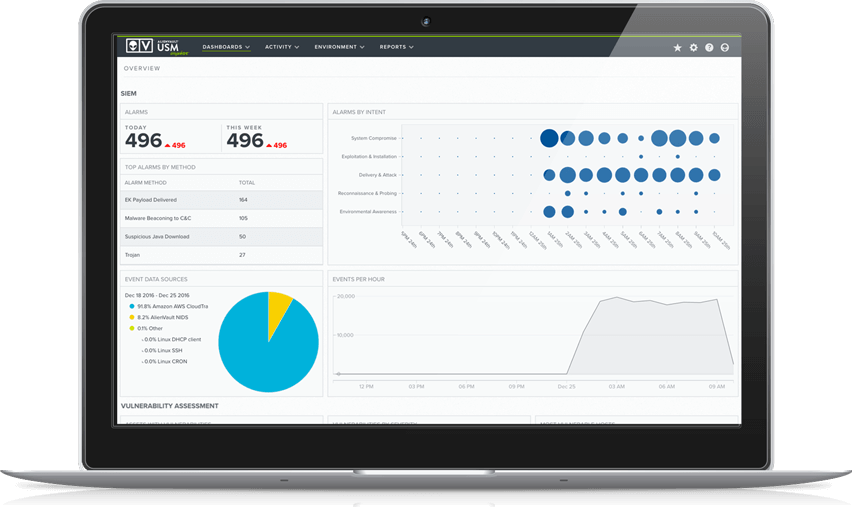
Centralize AWS security monitoring
USM Anywhere automatically collects and alerts on security data from critical AWS services such as CloudTrail, CloudWatch, and S3 and ELB access logs, centralizing and simplifying your AWS security monitoring.
Get threat intelligence built for AWS
Alien Labs’ threat intelligence includes AWS-specific correlation rules, so you can detect the latest threats, vulnerabilities, misconfigurations, and anomalous behaviors in your AWS environment.
Scale security with your cloud
USM Anywhere is a cloud-hosted SaaS platform that readily scales as your IT environment evolves. It’s fast and easy to deploy with no hardware to install.
Eliminate blind spots and shadow IT
Centrally monitor your multi-cloud and on-prem assets with a unified platform to ensure continuous threat coverage and the elimination of shadow IT as you migrate data and services to the cloud.
Discover DevOps-friendly security
Support your agile development with automated security monitoring across build, test, and production environments and leverage our integrations with DevOps tools like PagerDuty, Slack, Jira and others.
Simplify compliance in the cloud
Ensure your AWS environment adheres to key regulatory or industry compliance mandates, such as PCI DSS, HIPAA, or GDPR. Learn how USM Anywhere simplifies IT security compliance in AWS.
Secure your AWS environment
USM Anywhere provides complete cloud security management for your AWS environments. It includes all of the essential capabilities for monitoring cloud security and quickly identifying malicious or suspicious activity in your AWS cloud infrastructure.